Cryptanalysis of the Lorenz cipher
Cryptanalysis of the Lorenz cipher was the process that enabled the British to read high-level German army messages during World War II. The British Government Code and Cypher School (GC&CS) at Bletchley Park decrypted many communications between the Oberkommando der Wehrmacht (OKW, German High Command) in Berlin and their army commands throughout occupied Europe, some of which were signed "Adolf Hitler, Führer".[3] These were intercepted non-Morse radio transmissions that had been enciphered by the Lorenz SZ teleprinter rotor stream cipher attachments. Decrypts of this traffic became an important source of "Ultra" intelligence, which contributed significantly to Allied victory.[4]
| Time | Event |
|---|---|
| September 1939 | War breaks out in Europe. |
| Second half of 1940 | First non-Morse transmissions intercepted. |
| June 1941 | First experimental SZ40 Tunny link started with alphabetic indicator. |
| August 1941 | Two long messages in depth yielded 3700 characters of key. |
| January 1942 |
|
| July 1942 | |
| October 1942 |
|
| November 1942 | "1 + 2 break in" invented by Bill Tutte. |
| February 1943 | More complex SZ42A introduced. |
| May 1943 | Heath Robinson delivered. |
| June 1943 | Newmanry founded. |
| December 1943 | Colossus I working at Dollis Hill prior to delivery to Bletchley Park.[2] |
| February 1944 | First use of Colossus I for a real job. |
| March 1944 | Four Colossi (Mark 2) ordered. |
| April 1944 | Order for further Colossi increased to 12. |
| June 1944 |
|
| August 1944 | Cam settings on all Lorenz wheels changed daily. |
| May 1945 |
|
For its high-level secret messages, the German armed services enciphered each character using various online Geheimschreiber (secret writer) stream cipher machines at both ends of a telegraph link using the 5-bit International Telegraphy Alphabet No. 2 (ITA2). These machines were subsequently discovered to be the Lorenz SZ (SZ for Schlüssel-Zusatz, meaning "cipher attachment") for the army,[5] the Siemens and Halske T52 for the air force and the Siemens T43, which was little used and never broken by the Allies.[6]
Bletchley Park decrypts of messages enciphered with the Enigma machines revealed that the Germans called one of their wireless teleprinter transmission systems "Sägefisch" (sawfish),[7] which led British cryptographers to refer to encrypted German radiotelegraphic traffic as "Fish".[5] "Tunny" (tunafish) was the name given to the first non-Morse link, and it was subsequently used for the cipher machines and their traffic.[8]
As with the entirely separate cryptanalysis of the Enigma, it was German operational shortcomings that allowed the initial diagnosis of the system, and a way into decryption.[9] Unlike Enigma, no physical machine reached allied hands until the very end of the war in Europe, long after wholesale decryption had been established.[10][11] The problems of decrypting Tunny messages led to the development of "Colossus", the world's first electronic, programmable digital computer, ten of which were in use by the end of the war,[12][13] by which time some 90% of selected Tunny messages were being decrypted at Bletchley Park.[14]
Albert W. Small, a cryptanalyst from the US Army Signal Corps who was seconded to Bletchley Park and worked on Tunny, said in his December 1944 report back to Arlington Hall that:
Daily solutions of Fish messages at GC&CS reflect a background of British mathematical genius, superb engineering ability, and solid common sense. Each of these has been a necessary factor. Each could have been overemphasised or underemphasised to the detriment of the solutions; a remarkable fact is that the fusion of the elements has been apparently in perfect proportion. The result is an outstanding contribution to cryptanalytic science.[15]
The German Tunny machines
The Lorenz SZ cipher attachments implemented a Vernam stream cipher, using a complex array of twelve wheels that delivered what should have been a cryptographically secure pseudorandom number as a key stream. The key stream was combined with the plaintext to produce the ciphertext at the transmitting end using the exclusive or (XOR) function. At the receiving end, an identically configured machine produced the same key stream which was combined with the ciphertext to produce the plaintext, i. e. the system implemented a symmetric-key algorithm.
The key stream was generated by ten of the twelve wheels. This was a product of XOR-ing the character generated by the right hand five wheels, the chi () wheels, and the left hand five, the psi () wheels. The chi wheels always moved on one position for every incoming ciphertext character, but the psi wheels did not.

The central two mu () or "motor" wheels determined whether or not the psi wheels rotated with a new character.[17][18] After each letter was enciphered either all five psi wheels moved on, or they remained still and the same letter of psi-key was used again. Like the chi wheels, the 61 wheel moved on after each character. When 61 had the cam in the active position and so generated x (before moving) 37 moved on once: when the cam was in the inactive position (before moving) 37 and the psi wheels stayed still.[19] On all but the earliest machines, there was an additional factor that played into the moving on or not of the psi wheels. These were of four different types and were called "Limitations" at Bletchley Park. All involved some aspect of the previous positions of the machine's wheels.[20]
The numbers of cams on the set of twelve wheels of the SZ42 machines totalled 501 and were co-prime with each other, giving an extremely long period before the key sequence repeated. Each cam could either be in a raised position, in which case it contributed x to the logic of the system, reversing the value of a bit, or in the lowered position, in which case it generated •.[10] The total possible number of patterns of raised cams was 2501 which is an astronomically large number.[21] In practice, however, about half of the cams on each wheel were in the raised position. Later, the Germans realized that if the number of raised cams was not very close to 50% there would be runs of xs and •s, a cryptographic weakness.[22][23]
The process of working out which of the 501 cams were in the raised position was called "wheel breaking" at Bletchley Park.[24] Deriving the start positions of the wheels for a particular transmission was termed "wheel setting" or simply "setting". The fact that the psi wheels all moved together, but not with every input character, was a major weakness of the machines that contributed to British cryptanalytical success.

Secure telegraphy
Electro-mechanical telegraphy was developed in the 1830s and 1840s, well before telephony, and operated worldwide by the time of the Second World War. An extensive system of cables linked sites within and between countries, with a standard voltage of −80 V indicating a "mark" and +80 V indicating a "space".[25] Where cable transmission became impracticable or inconvenient, such as for mobile German Army Units, radio transmission was used.
Teleprinters at each end of the circuit consisted of a keyboard and a printing mechanism, and very often a five-hole perforated paper-tape reading and punching mechanism. When used online, pressing an alphabet key at the transmitting end caused the relevant character to print at the receiving end. Commonly, however, the communication system involved the transmitting operator preparing a set of messages offline by punching them onto paper tape, and then going online only for the transmission of the messages recorded on the tape. The system would typically send some ten characters per second, and so occupy the line or the radio channel for a shorter period of time than for online typing.
The characters of the message were represented by the codes of the International Telegraphy Alphabet No. 2 (ITA2). The transmission medium, either wire or radio, used asynchronous serial communication with each character signaled by a start (space) impulse, 5 data impulses and 1½ stop (mark) impulses. At Bletchley Park mark impulses were signified by x and space impulses by •.[26] For example, the letter "H" would be coded as ••x•x.
| Pattern of impulses Mark = x, Space = • | Binary | Letter shift | Figure shift | BP 'shiftless' interpretation |
|---|---|---|---|---|
| ••.••• | 00000 | null | null | / |
| ••.x•• | 00100 | space | space | 9 |
| ••.x•x | 00101 | H | # | H |
| ••.••x | 00001 | T | 5 | T |
| ••.•xx | 00011 | O | 9 | O |
| ••.xxx | 00111 | M | . | M |
| ••.xx• | 00110 | N | , | N |
| ••.•x• | 00010 | CR | CR | 3 |
| •x.•x• | 01010 | R | 4 | R |
| •x.xx• | 01110 | C | : | C |
| •x.xxx | 01111 | V | ; | V |
| •x.•xx | 01011 | G | & | G |
| •x.••x | 01001 | L | ) | L |
| •x.x•x | 01101 | P | 0 | P |
| •x.x•• | 01100 | I | 8 | I |
| •x.••• | 01000 | LF | LF | 4 |
| xx.••• | 11000 | A | - | A |
| xx.x•• | 11100 | U | 7 | U |
| xx.x•x | 11101 | Q | 1 | Q |
| xx.••x | 11001 | W | 2 | W |
| xx.•xx | 11011 | FIGS | + or 5 | |
| xx.xxx | 11111 | LTRS | - or 8 | |
| xx.xx• | 11110 | K | ( | K |
| xx.•x• | 11010 | J | Bell | J |
| x•.•x• | 10010 | D | WRU | D |
| x•.xx• | 10110 | F | ! | F |
| x•.xxx | 10111 | X | / | X |
| x•.•xx | 10011 | B | ? | B |
| x•.••x | 10001 | Z | " | Z |
| x•.x•x | 10101 | Y | 6 | Y |
| x•.x•• | 10100 | S | ' | S |
| x•.••• | 10000 | E | 3 | E |
The figure shift (FIGS) and letter shift (LETRS) characters determined how the receiving end interpreted the string of characters up to the next shift character. Because of the danger of a shift character being corrupted, some operators would type a pair of shift characters when changing from letters to numbers or vice versa. So they would type 55M88 to represent a full stop.[28] Such doubling of characters was very helpful for the statistical cryptanalysis used at Bletchley Park. After encipherment, shift characters had no special meaning.
The speed of transmission of a radio-telegraph message was three or four times that of Morse code and a human listener could not interpret it. A standard teleprinter, however would produce the text of the message. The Lorenz cipher attachment changed the plaintext of the message into ciphertext that was uninterpretable to those without an identical machine identically set up. This was the challenge faced by the Bletchley Park codebreakers.
Interception
Intercepting Tunny transmissions presented substantial problems. As the transmitters were directional, most of the signals were quite weak at receivers in Britain. Furthermore, there were some 25 different frequencies used for these transmissions, and the frequency would sometimes be changed part way through. After the initial discovery of the non-Morse signals in 1940, a radio intercept station called the Foreign Office Research and Development Establishment was set up on a hill at Ivy Farm at Knockholt in Kent, specifically to intercept this traffic.[29][30] The centre was headed by Harold Kenworthy, had 30 receiving sets and employed some 600 staff. It became fully operational early in 1943.

Because a single missed or corrupted character could make decryption impossible, the greatest accuracy was required.[31] The undulator technology used to record the impulses had originally been developed for high-speed Morse. It produced a visible record of the impulses on narrow paper tape. This was then read by people employed as "slip readers" who interpreted the peaks and troughs as the marks and spaces of ITA2 characters.[32] Perforated paper tape was then produced for telegraphic transmission to Bletchley Park where it was punched out.[33]
The Vernam cipher
The Vernam cipher implemented by the Lorenz SZ machines utilizes the Boolean "exclusive or" (XOR) function, symbolised by ⊕ and verbalised as "A or B but not both". This is represented by the following truth table, where x represents "true" and • represents "false".
| INPUT | OUTPUT | |
| A | B | A ⊕ B |
| • | • | • |
| • | x | x |
| x | • | x |
| x | x | • |
Other names for this function are: exclusive disjunction, not equal (NEQ), and modulo 2 addition (without "carry") and subtraction (without "borrow"). Modulo 2 addition and subtraction are identical. Some descriptions of Tunny decryption refer to addition and some to differencing, i.e. subtraction, but they mean the same thing.
Reciprocity is a desirable feature of a machine cipher so that the same machine with the same settings can be used either for enciphering or for deciphering. The Vernam cipher achieves this, as combining the stream of plaintext characters with the key stream produces the ciphertext, and combining the same key with the ciphertext regenerates the plaintext.[34]
Symbolically:
- Plaintext ⊕ Key = Ciphertext
and
- Ciphertext ⊕ Key = Plaintext
Vernam's original idea was to use conventional telegraphy practice, with a paper tape of the plaintext combined with a paper tape of the key at the transmitting end, and an identical key tape combined with the ciphertext signal at the receiving end. Each pair of key tapes would have been unique (a one-time tape), but generating and distributing such tapes presented considerable practical difficulties. In the 1920s four men in different countries invented rotor Vernam cipher machines to produce a key stream to act instead of a key tape. The Lorenz SZ40/42 was one of these.[35]
Security features
.svg.png.webp)
A monoalphabetic substitution cipher such as the Caesar cipher can easily be broken, given a reasonable amount of ciphertext. This is achieved by frequency analysis of the different letters of the ciphertext, and comparing the result with the known letter frequency distribution of the plaintext.[36]
With a polyalphabetic cipher, there is a different substitution alphabet for each successive character. So a frequency analysis shows an approximately uniform distribution, such as that obtained from a (pseudo) random number generator. However, because one set of Lorenz wheels turned with every character while the other did not, the machine did not disguise the pattern in the use of adjacent characters in the German plaintext. Alan Turing discovered this weakness and invented the differencing technique described below to exploit it.[37]
The pattern of which of the cams were in the raised position, and which in the lowered position was changed daily on the motor wheels (37 and 61). The chi wheel cam patterns were initially changed monthly. The psi wheel patterns were changed quarterly until October 1942 when the frequency was increased to monthly, and then to daily on 1 August 1944, when the frequency of changing the chi wheel patterns was also changed to daily.[38]
The number of start positions of the wheels was 43×47×51×53×59×37×61×41×31×29×26×23 which is approximately 1.6×1019 (16 billion billion), far too large a number for cryptanalysts to try an exhaustive "brute-force attack". Sometimes the Lorenz operators disobeyed instructions and two messages were transmitted with the same start positions, a phenomenon termed a "depth". The method by which the transmitting operator told the receiving operator the wheel settings that he had chosen for the message which he was about to transmit was termed the "indicator" at Bletchley Park.
In August 1942, the formulaic starts to the messages, which were useful to cryptanalysts, were replaced by some irrelevant text, which made identifying the true message somewhat harder. This new material was dubbed quatsch (German for "nonsense") at Bletchley Park.[39]
During the phase of the experimental transmissions, the indicator consisted of twelve German forenames, the initial letters of which indicated the position to which the operators turned the twelve wheels. As well as showing when two transmissions were fully in depth, it also allowed the identification of partial depths where two indicators differed only in one or two wheel positions. From October 1942 the indicator system changed to the sending operator transmitting the unenciphered letters QEP[40] followed by a two digit number. This number was taken serially from a code book that had been issued to both operators and gave, for each QEP number, the settings of the twelve wheels. The books were replaced when they had been used up, but between replacements, complete depths could be identified by the re-use of a QEP number on a particular Tunny link.[41]
Diagnosis
| P | plaintext |
| K | key – the sequence of characters XOR'ed (added) to the plaintext to give the ciphertext |
| chi component of key | |
| psi component of key | |
| extended psi – the actual sequence of characters added by the psi wheels, including those when they do not advance[43] | |
| Z | ciphertext |
| D | de-chi — the ciphertext with the chi component of the key removed |
| Δ | any of the above XOR'ed with its successor character or bit[44] |
| ⊕ | the XOR operation |
The first step in breaking a new cipher is to diagnose the logic of the processes of encryption and decryption. In the case of a machine cipher such as Tunny, this entailed establishing the logical structure and hence functioning of the machine. This was achieved without the benefit of seeing a machine—which only happened in 1945, shortly before the allied victory in Europe.[45] The enciphering system was very good at ensuring that the ciphertext Z contained no statistical, periodic or linguistic characteristics to distinguish it from random. However this did not apply to K, , and D, which was the weakness that meant that Tunny keys could be solved.[46]
During the experimental period of Tunny transmissions when the twelve-letter indicator system was in use, John Tiltman, Bletchley Park's veteran and remarkably gifted cryptanalyst, studied the Tunny ciphertexts and identified that they used a Vernam cipher.
When two transmissions (a and b) use the same key, i.e. they are in depth, combining them eliminates the effect of the key.[47] Let us call the two ciphertexts Za and Zb, the key K and the two plaintexts Pa and Pb. We then have:
- Za ⊕ Zb = Pa ⊕ Pb
If the two plaintexts can be worked out, the key can be recovered from either ciphertext-plaintext pair e.g.:
- Za ⊕ Pa = K or
Zb ⊕ Pb = K
- Za ⊕ Pa = K or
On 31 August 1941, two long messages were received that had the same indicator HQIBPEXEZMUG. The first seven characters of these two ciphertexts were the same, but the second message was shorter. The first 15 characters of the two messages were as follows:
| Za | JSH5N ZYZY5 GLFRG |
| Zb | JSH5N ZYMFS /883I |
| Za ⊕ Zb | ///// //FOU GFL4M |
John Tiltman tried various likely pieces of plaintext, i.e. a "cribs", against the Za ⊕ Zb string and found that the first plaintext message started with the German word SPRUCHNUMMER (message number). In the second plaintext, the operator had used the common abbreviation NR for NUMMER. There were more abbreviations in the second message, and the punctuation sometimes differed. This allowed Tiltman to work out, over ten days, the plaintext of both messages, as a sequence of plaintext characters discovered in Pa, could then be tried against Pb and vice versa.[48] In turn, this yielded almost 4000 characters of key.[49]
Members of the Research Section worked on this key to try to derive a mathematical description of the key generating process, but without success. Bill Tutte joined the section in October 1941 and was given the task. He had read chemistry and mathematics at Trinity College, Cambridge before being recruited to Bletchley Park. At his training course, he had been taught the Kasiski examination technique of writing out a key on squared paper with a new row after a defined number of characters that was suspected of being the frequency of repetition of the key. If this number was correct, the columns of the matrix would show more repetitions of sequences of characters than chance alone.
Tutte thought that it was possible that, rather than using this technique on the whole letters of the key, which were likely to have a long frequency of repetition, it might be worth trying it on only one impulse (bit) on the grounds that "the part might be cryptographically simpler than the whole".[50] Given that the Tunny indicators used 25 letters (excluding J) for 11 of the positions, but only 23 letters for the twelfth, he tried Kasiski's technique on the first impulse of the key characters using a repetition of 25 × 23 = 575. This did not produce a large number of repetitions in the columns, but Tutte did observe the phenomenon on a diagonal. He therefore tried again with 574, which showed up repeats in the columns. Recognising that the prime factors of this number are 2, 7 and 41, he tried again with a period of 41 and "got a rectangle of dots and crosses that was replete with repetitions".[51]
It was clear, however, that the first impulse of the key was more complicated than that produced by a single wheel of 41 positions. Tutte called this component of the key 1 (chi). He figured that there was another component, which was XOR-ed with this, that did not always change with each new character, and that this was the product of a wheel that he called 1 (psi). The same applied for each of the five impulses—indicated here by subscripts. So for a single character, the key K consisted of two components:
- K = ⊕ .
The actual sequence of characters added by the psi wheels, including those when they do not advance, was referred to as the extended psi,[43] and symbolised by '
- K = ⊕ ' .
Tutte's derivation of the component was made possible by the fact that dots were more likely than not to be followed by dots, and crosses more likely than not to be followed by crosses. This was a product of a weakness in the German key setting, which they later stopped. Once Tutte had made this breakthrough, the rest of the Research Section joined in to study the other impulses, and it was established that the five wheels all moved together under the control of two (mu or "motor") wheels.
Diagnosing the functioning of the Tunny machine in this way was a truly remarkable cryptanalytical achievement, and was described when Tutte was inducted as Officer of the Order of Canada in October 2001, as "one of the greatest intellectual feats of World War II".[52]
Turingery
In July 1942 Alan Turing spent a few weeks in the Research Section.[53] He had become interested in the problem of breaking Tunny from the keys that had been obtained from depths.[54] In July, he developed a method of deriving the cam settings ("wheel breaking") from a length of key. It became known as "Turingery"[55] (playfully dubbed "Turingismus" by Peter Ericsson, Peter Hilton and Donald Michie[54]) and introduced the important method of "differencing" on which much of the rest of solving Tunny keys in the absence of depths, was based.[55]
Differencing
The search was on for a process that would manipulate the ciphertext or key to produce a frequency distribution of characters that departed from the uniformity that the enciphering process aimed to achieve. Turing worked out that the XOR combination of the values of successive (adjacent) characters in a stream of ciphertext or key, emphasised any departures from a uniform distribution.[55][56] The resultant stream was called the difference (symbolised by the Greek letter "delta" Δ)[57] because XOR is the same as modulo 2 subtraction. So, for a stream of characters S, the difference ΔS was obtained as follows, where underline indicates the succeeding character:
- ΔS = S ⊕ S
The stream S may be ciphertext Z, plaintext P, key K or either of its two components and . The relationship amongst these elements still applies when they are differenced. For example, as well as:
- K = ⊕
It is the case that:
- ΔK = Δ ⊕ Δ
Similarly for the ciphertext, plaintext and key components:
- ΔZ = ΔP ⊕ Δ ⊕ Δ
So:
- ΔP = ΔZ ⊕ Δ ⊕ Δ
The reason that differencing provided a way into Tunny, was that although the frequency distribution of characters in the ciphertext could not be distinguished from a random stream, the same was not true for a version of the ciphertext from which the chi element of the key had been removed. This is because, where the plaintext contained a repeated character and the psi wheels did not move on, the differenced psi character (Δ) would be the null character ('/' at Bletchley Park). When XOR-ed with any character, this character has no effect, so in these circumstances, ΔK = Δ. The ciphertext modified by the removal of the chi component of the key was called the de-chi D at Bletchley Park,[58] and the process of removing it as "de-chi-ing". Similarly for the removal of the psi component which was known as "de-psi-ing" (or "deep sighing" when it was particularly difficult).[59]
So the delta de-chi ΔD was:
- ΔD = ΔZ ⊕ Δ
Repeated characters in the plaintext were more frequent both because of the characteristics of German (EE, TT, LL and SS are relatively common),[60] and because telegraphists frequently repeated the figures-shift and letters-shift characters[61] as their loss in an ordinary telegraph transmission could lead to gibberish.[62]
To quote the General Report on Tunny:
Turingery introduced the principle that the key differenced at one, now called ΔΚ, could yield information unobtainable from ordinary key. This Δ principle was to be the fundamental basis of nearly all statistical methods of wheel-breaking and setting.[55]
Differencing was applied to each of the impulses of the ITA2 coded characters.[63] So, for the first impulse, that was enciphered by wheels 1 and 1, differenced at one:
- ΔK1 = K1 ⊕ K1
And for the second impulse:
- ΔK2 = K2 ⊕ K2
And so on.
The periodicity of the chi and psi wheels for each impulse (41 and 43 respectively for the first impulse) is also reflected in the pattern of ΔK. However, given that the psi wheels did not advance for every input character, as did the chi wheels, it was not simply a repetition of the pattern every 41 × 43 = 1763 characters for ΔK1, but a more complex sequence.
Turing's method
Turing's method of deriving the cam settings of the wheels from a length of key obtained from a depth, involved an iterative process. Given that the delta psi character was the null character '/' half of the time on average, an assumption that ΔK = Δ had a 50% chance of being correct. The process started by treating a particular ΔK character as being the Δ for that position. The resulting putative bit pattern of x and • for each chi wheel, was recorded on a sheet of paper that contained as many columns as there were characters in the key, and five rows representing the five impulses of the Δ. Given the knowledge from Tutte's work, of the periodicity of each of the wheels, this allowed the propagation of these values at the appropriate positions in the rest of the key.
A set of five sheets, one for each of the chi wheels, was also prepared. These contained a set of columns corresponding in number to the cams for the appropriate chi wheel, and were referred to as a 'cage'. So the 3 cage had 29 such columns.[64] Successive 'guesses' of Δ values then produced further putative cam state values. These might either agree or disagree with previous assumptions, and a count of agreements and disagreements was made on these sheets. Where disagreements substantially outweighed agreements, the assumption was made that the Δ character was not the null character '/', so the relevant assumption was discounted. Progressively, all the cam settings of the chi wheels were deduced, and from them, the psi and motor wheel cam settings.
As experience of the method developed, improvements were made that allowed it to be used with much shorter lengths of key than the original 500 or so characters."[55]
Testery
The Testery was the section at Bletchley Park that performed the bulk of the work involved in decrypting Tunny messages.[65] By July 1942, the volume of traffic was building up considerably. A new section was therefore set up, led by Ralph Tester—hence the name. The staff consisted mainly of ex-members of the Research Section,[1] and included Peter Ericsson, Peter Hilton, Denis Oswald and Jerry Roberts.[66] The Testery's methods were almost entirely manual, both before and after the introduction of automated methods in the Newmanry to supplement and speed up their work.[14][1]
The first phase of the work of the Testery ran from July to October, with the predominant method of decryption being based on depths and partial depths.[67] After ten days, however, the formulaic start of the messages was replaced by nonsensical quatsch, making decryption more difficult. This period was productive nonetheless, even though each decryption took considerable time. Finally, in September, a depth was received that allowed Turing's method of wheel breaking, "Turingery", to be used, leading to the ability to start reading current traffic. Extensive data about the statistical characteristics of the language of the messages was compiled, and the collection of cribs extended.[55]
In late October 1942 the original, experimental Tunny link was closed and two new links (Codfish and Octopus) were opened. With these and subsequent links, the 12-letter indicator system of specifying the message key was replaced by the QEP system. This meant that only full depths could be recognised—from identical QEP numbers—which led to a considerable reduction in traffic decrypted.
Once the Newmanry became operational in June 1943, the nature of the work performed in the Testery changed, with decrypts, and wheel breaking no longer relying on depths.
British Tunny
The so-called "British Tunny Machine" was a device that exactly replicated the functions of the SZ40/42 machines. It was used to produce the German cleartext from a ciphertext tape, after the cam settings had been determined.[68] The functional design was produced at Bletchley Park where ten Testery Tunnies were in use by the end of the war. It was designed and built in Tommy Flowers' laboratory at the General Post Office Research Station at Dollis Hill by Gil Hayward, "Doc" Coombs, Bill Chandler and Sid Broadhurst.[69] It was mainly built from standard British telephone exchange electro-mechanical equipment such as relays and uniselectors. Input and output was by means of a teleprinter with paper tape reading and punching.[70] These machines were used in both the Testery and later the Newmanry. Dorothy Du Boisson who was a machine operator and a member of the Women's Royal Naval Service (Wren), described plugging up the settings as being like operating an old fashioned telephone exchange and that she received electric shocks in the process.[71]
When Flowers was invited by Hayward to try the first British Tunny machine at Dollis Hill by typing in the standard test phrase: "Now is the time for all good men to come to the aid of the party", he much appreciated that the rotor functions had been set up to provide the following Wordsworthian output:[72]
| Input | NOW IS THE TIME FOR ALL GOOD MEN TO COME TO THE AID OF THE PARTY |
| Output | I WANDERED LONELY AS A CLOUD THAT FLOATS ON HIGH OER VALES AND H |
Additional features were added to the British Tunnies to simplify their operation. Further refinements were made for the versions used in the Newmanry, the third Tunny being equipped to produce de-chi tapes.[73][74]
Newmanry
The Newmanry was a section set up under Max Newman in December 1942 to look into the possibility of assisting the work of the Testery by automating parts of the processes of decrypting Tunny messages. Newman had been working with Gerry Morgan, head of the Research Section on ways of breaking Tunny when Bill Tutte approached them in November 1942 with the idea of what became known as the "1+2 break in".[75] This was recognised as being feasible, but only if automated.
Newman produced a functional specification of what was to become the "Heath Robinson" machine.[75] He recruited the Post Office Research Station at Dollis Hill, and Dr C.E. Wynn-Williams at the Telecommunications Research Establishment (TRE) at Malvern to implement his idea. Work on the engineering design started in January 1943 and the first machine was delivered in June. The staff at that time consisted of Newman, Donald Michie, Jack Good, two engineers and 16 Wrens. By the end of the war the Newmanry contained three Robinson machines, ten Colossus Computers and a number of British Tunnies. The staff were 26 cryptographers, 28 engineers and 275 Wrens.[76]
The automation of these processes required the processing of large quantities of punched paper tape such as those on which the enciphered messages were received. Absolute accuracy of these tapes and their transcription was essential, as a single character in error could invalidate or corrupt a huge amount of work. Jack Good introduced the maxim "If it's not checked it's wrong".[77]
The "1+2 break in"
W. T. Tutte developed a way of exploiting the non-uniformity of bigrams (adjacent letters) in the German plaintext using the differenced cyphertext and key components. His method was called the "1+2 break in," or "double-delta attack".[78] The essence of this method was to find the initial settings of the chi component of the key by exhaustively trying all positions of its combination with the ciphertext, and looking for evidence of the non-uniformity that reflected the characteristics of the original plaintext.[79] [80] The wheel breaking process had to have successfully produced the current cam settings to allow the relevant sequence of characters of the chi wheels to be generated. It was totally impracticable to generate the 22 million characters from all five of the chi wheels, so it was initially limited to 41 × 31 = 1271 from the first two.
Given that for each of the five impulses i:
- Zi = i ⊕ i ⊕ Pi
and hence
- Pi = Zi ⊕ i ⊕ i
for the first two impulses:
- (P1 ⊕ P2) = (Z1 ⊕ Z2) ⊕ (1 ⊕ 2) ⊕ (1 ⊕ 2)
Calculating a putative P1 ⊕ P2 in this way for each starting point of the 1 ⊕ 2 sequence would yield xs and •s with, in the long run, a greater proportion of •s when the correct starting point had been used. Tutte knew, however, that using the differenced (∆) values amplified this effect[81] because any repeated characters in the plaintext would always generate •, and similarly ∆1 ⊕ ∆2 would generate • whenever the psi wheels did not move on, and about half of the time when they did - some 70% overall.
Tutte analyzed a decrypted ciphertext with the differenced version of the above function:
- (∆Z1 ⊕ ∆Z2) ⊕ (∆1 ⊕ ∆2) ⊕ (∆1 ⊕ ∆2)
and found that it generated • some 55% of the time.[82] Given the nature of the contribution of the psi wheels, the alignment of chi-stream with the ciphertext that gave the highest count of •s from (∆Z1 ⊕ ∆Z2 ⊕ ∆1 ⊕ ∆2) was the one that was most likely to be correct.[83] This technique could be applied to any pair of impulses and so provided the basis of an automated approach to obtaining the de-chi (D) of a ciphertext, from which the psi component could be removed by manual methods.
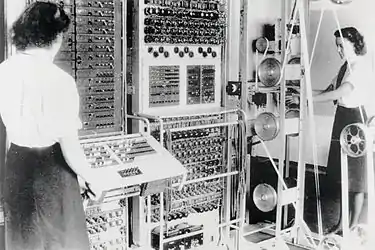
Robinsons
Heath Robinson was the first machine produced to automate Tutte's 1+2 method. It was given the name by the Wrens who operated it, after cartoonist William Heath Robinson, who drew immensely complicated mechanical devices for simple tasks, similar to the American cartoonist Rube Goldberg.
The functional specification of the machine was produced by Max Newman. The main engineering design was the work of Frank Morrell[84] at the Post Office Research Station at Dollis Hill in North London, with his colleague Tommy Flowers designing the "Combining Unit". Dr C. E. Wynn-Williams from the Telecommunications Research Establishment at Malvern produced the high-speed electronic valve and relay counters.[85] Construction started in January 1943,[86] the prototype machine was in use at Bletchley Park in June.[87]
The main parts of the machine were:
- a tape transport and reading mechanism (dubbed the "bedstead" because of its resemblance to an upended metal bed frame) that ran the looped key and message tapes at between 1000 and 2000 characters per second;
- a combining unit that implemented the logic of Tutte's method;
- a counting unit that counted the number of •s, and if it exceeded a pre-set total, displayed or printed it.
The prototype machine was effective despite a number of serious shortcomings. Most of these were progressively overcome in the development of what became known as "Old Robinson".[88]
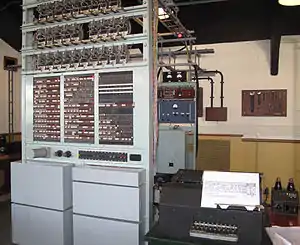
Colossus

Tommy Flowers' experience with Heath Robinson, and his previous, unique experience of thermionic valves (vacuum tubes) led him to realize that a better machine could be produced using electronics. Instead of the key stream being read from a punched paper tape, an electronically generated key stream could allow much faster and more flexible processing. Flowers' suggestion that this could be achieved with a machine that was entirely electronic and would contain between one and two thousand valves, was treated with incredulity at both the Telecommunications Research Establishment and at Bletchley Park, as it was thought that it would be "too unreliable to do useful work". He did, however, have the support of the Controller of Research at Dollis Hill, W Gordon Radley,[89] and he implemented these ideas producing Colossus, the world's first electronic, digital, computing machine that was at all programmable, in the remarkably short time of ten months.[90] In this he was assisted by his colleagues at the Post Office Research Station Dollis Hill: Sidney Broadhurst, William Chandler, Allen Coombs and Harry Fensom.
The prototype Mark 1 Colossus (Colossus I), with its 1500 valves, became operational at Dollis Hill in December 1943[2] and was in use at Bletchley Park by February 1944. This processed the message at 5000 characters per second using the impulse from reading the tape's sprocket holes to act as the clock signal. It quickly became evident that this was a huge leap forward in cryptanalysis of Tunny. Further Colossus machines were ordered and the orders for more Robinsons cancelled. An improved Mark 2 Colossus (Colossus II) contained 2400 valves and first worked at Bletchley Park on 1 June 1944, just in time for the D-day Normandy landings.
The main parts of this machine were:[91]
- a tape transport and reading mechanism (the "bedstead") that ran the message tape in a loop at 5000 characters per second;
- a unit that generated the key stream electronically;
- five parallel processing units that could be programmed to perform a large range of Boolean operations;
- five counting units that each counted the number of •s or xs, and if it exceeded a pre-set total, printed it out.
The five parallel processing units allowed Tutte's "1+2 break in" and other functions to be run at an effective speed of 25,000 characters per second by the use of circuitry invented by Flowers that would now be called a shift register. Donald Michie worked out a method of using Colossus to assist in wheel breaking as well as for wheel setting.[92] This was then implemented in special hardware on later Colossi.
A total of ten Colossus computers were in use and an eleventh was being commissioned at the end of the war in Europe (VE-Day).[93]
Special machines
As well as the commercially produced teleprinters and re-perforators, a number of other machines were built to assist in the preparation and checking of tapes in the Newmanry and Testery.[94][95] The approximate complement as of May 1945 was as follows.
| Name | Function | Testery | Newmanry |
|---|---|---|---|
| Super Robinson | Used for crib runs in which two tapes were compared in all positions. Contained some valves. | 2 | |
| Colossus Mk.2 | Counted a condition involving a message tape and an electronically generated key character stream imitating the various Tunny wheels in different relative positions ("stepping").[96] Contained some 2,400 valves. | 10 | |
| Dragons | Used for setting short cribs by "crib-dragging" (hence the name).[97][98] | 2 | |
| Aquarius | A machine under development at the war's end for the "go-backs" of the SZ42B, which stored the contents of the message tape in a large bank of capacitors that acted as an electronic memory.[99] | 1 | |
| Proteus | A machine for utilising depths that was under construction at the war's end but was not completed. | ||
| Decoding Machines | Translated from ciphertext typed in, to plaintext printed out. Some of the later ones were speeded up with the use of a few valves.[100] A number of modified machines were produced for the Newmanry | 13 | |
| Tunnies | See British Tunny above | 3 | |
| Miles | A set of increasingly complex machines (A, B, C, D) that read two or more tapes and combined them in a variety of ways to produce an output tape.[101] | 3 | |
| Garbo | Similar to Junior, but with a Delta'ing facility – used for rectangling.[102] | 3 | |
| Juniors | For printing tapes via a plug panel to change characters as necessary, used to print de-chis.[74] | 4 | |
| Insert machines | Similar to Angel, but with a device for making corrections by hand. | 2 | |
| Angels | Copied tapes. | 4 | |
| Hand perforators | Generated tape from a keyboard. | 2 | |
| Hand counters | Measured text length. | 6 | |
| Stickers (hot) | Bostik and benzene was used for sticking tapes to make a loop. The tape to be stuck was inserted between two electrically heated plates and the benzene evaporated. | 3 | |
| Stickers (cold) | Stuck tapes without heating. | 6 |
Steps in wheel setting
Working out the start position of the chi () wheels required first that their cam settings had been determined by "wheel breaking". Initially, this was achieved by two messages having been sent in depth.
The number of start positions for the first two wheels, 1 and 2 was 41×31 = 1271. The first step was to try all of these start positions against the message tape. This was Tutte's "1+2 break in" which involved computing (∆Z1 ⊕ ∆Z2 ⊕ ∆1 ⊕ ∆2)—which gives a putative (∆D1 ⊕ ∆D2)—and counting the number of times this gave •. Incorrect starting positions would, on average, give a dot count of 50% of the message length. On average, the dot count for a correct starting point would be 54%, but there was inevitably a considerable spread of values around these averages.[83]
Both Heath Robinson, which was developed into what became known as "Old Robinson", and Colossus were designed to automate this process. Statistical theory allowed the derivation of measures of how far any count was from the 50% expected with an incorrect starting point for the chi wheels. This measure of deviation from randomness was called sigma. Starting points that gave a count of less than 2.5 × sigma, named the "set total", were not printed out.[103] The ideal for a run to set 1 and 2 was that a single pair of trial values produced one outstanding value for sigma thus identifying the start positions of the first two chi wheels. An example of the output from such a run on a Mark 2 Colossus with its five counters: a, b, c, d and e, is given below.
| 1 | 2 | Counter | Count | Operator's notes on the output |
|---|---|---|---|---|
| 06 | 11 | a | 4921 | |
| 06 | 13 | a | 4948 | |
| 02 | 16 | e | 4977 | |
| 05 | 18 | b | 4926 | |
| 02 | 20 | e | 4954 | |
| 05 | 22 | b | 4914 | |
| 03 | 25 | d | 4925 | |
| 02 | 26 | e | 5015 | ← 4.6 sigma |
| 19 | 26 | c | 4928 | |
| 25 | 19 | b | 4930 | |
| 25 | 21 | b | 5038 | ← 5.1 sigma |
| 29 | 18 | c | 4946 | |
| 36 | 13 | a | 4955 | |
| 35 | 18 | b | 4926 | |
| 36 | 21 | a | 5384 | ← 12.2 sigma ch 1 2 ! ! |
| 36 | 25 | a | 4965 | |
| 36 | 29 | a | 5013 | |
| 38 | 08 | d | 4933 | |
With an average-sized message, this would take about eight minutes. However, by utilising the parallelism of the Mark 2 Colossus, the number of times the message had to be read could be reduced by a factor of five, from 1271 to 255. [105] Having identified possible 1, 2 start positions, the next step was to try to find the start positions for the other chi wheels. In the example given above, there is a single setting of 1 = 36 and 2 = 21 whose sigma value makes it stand out from the rest. This was not always the case, and Small enumerates 36 different further runs that might be tried according to the result of the 1, 2 run.[106] At first the choices in this iterative process were made by the cryptanalyst sitting at the typewriter output, and calling out instructions to the Wren operators. Max Newman devised a decision tree and then set Jack Good and Donald Michie the task of devising others.[107] These were used by the Wrens without recourse to the cryptanalysts if certain criteria were met.[108]
In the above one of Small's examples, the next run was with the first two chi wheels set to the start positions found and three separate parallel explorations of the remaining three chi wheels. Such a run was called a "short run" and took about two minutes.[105]
| 1 | 2 | 3 | 4 | 5 | Counter | Count | Operator's notes on the output |
|---|---|---|---|---|---|---|---|
| 36 | 21 | 01 | a | 2938 | ← 6.8 rho ! 3 ! | ||
| 36 | 21 | 01 | b | 2763 | |||
| 36 | 21 | 01 | c | 2803 | |||
| 36 | 21 | 02 | b | 2733 | |||
| 36 | 21 | 04 | c | 3003 | ← 8.6 rho ! 5 ! | ||
| 36 | 21 | 06 | a | 2740 | |||
| 36 | 21 | 07 | c | 2750 | |||
| 36 | 21 | 09 | b | 2811 | |||
| 36 | 21 | 11 | a | 2751 | |||
| 36 | 21 | 12 | c | 2759 | |||
| 36 | 21 | 14 | c | 2733 | |||
| 36 | 21 | 16 | a | 2743 | |||
| 36 | 21 | 19 | b | 3093 | ← 11.1 rho ! 4 ! | ||
| 36 | 21 | 20 | a | 2785 | |||
| 36 | 21 | 22 | b | 2823 | |||
| 36 | 21 | 24 | a | 2740 | |||
| 36 | 21 | 25 | b | 2796 | |||
| 36 | 21 | 01 | b | 2763 | |||
| 36 | 21 | 07 | c | 2750 | |||
So the probable start positions for the chi wheels are: 1 = 36, 2 = 21, 3 = 01, 4 = 19, 5 = 04. These had to be verified before the de-chi (D) message was passed to the Testery. This involved Colossus performing a count of the frequency of the 32 characters in ΔD. Small describes the check of the frequency count of the ΔD characters as being the "acid test",[110] and that practically every cryptanalyst and Wren in the Newmanry and Testery knew the contents of the following table by heart.
| Char. | Count | Char. | Count | Char. | Count | Char. | Count | |||
|---|---|---|---|---|---|---|---|---|---|---|
| / | 1.28 | R | 0.92 | A | 0.96 | D | 0.89 | |||
| 9 | 1.10 | C | 0.90 | U | 1.24 | F | 1.00 | |||
| H | 1.02 | V | 0.94 | Q | 1.01 | X | 0.87 | |||
| T | 0.99 | G | 1.00 | W | 0.89 | B | 0.82 | |||
| O | 1.04 | L | 0.92 | 5 | 1.43 | Z | 0.89 | |||
| M | 1.00 | P | 0.96 | 8 | 1.12 | Y | 0.97 | |||
| N | 1.00 | I | 0.96 | K | 0.89 | S | 1.04 | |||
| 3 | 1.13 | 4 | 0.90 | J | 1.03 | E | 0.89 |
If the derived start points of the chi wheels passed this test, the de-chi-ed message was passed to the Testery where manual methods were used to derive the psi and motor settings. As Small remarked, the work in the Newmanry took a great amount of statistical science, whereas that in the Testery took much knowledge of language and was of great interest as an art. Cryptanalyst Jerry Roberts made the point that this Testery work was a greater load on staff than the automated processes in the Newmanry.[14]
See also
Notes and references
- Good, Michie & Timms 1945, 1 Introduction: 14 Organisation, 14A Expansion and Growth, (b) Three periods, p. 28.
- Flowers 1983, p. 245.
- McKay 2010, p. 263 quoting Jerry Roberts.
- Hinsley 1993, p. 8.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11A Fish Machines, (c) The German Ciphered Teleprinter, p. 4.
- Weierud 2006, p. 307.
- Gannon 2007, p. 103.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11A Fish Machines, (c) The German Ciphered Teleprinter, p. 5.
- Copeland 2006, p. 45.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, (j) Mechanical Aspects, p. 10.
- Good 1993, pp. 162,163.
- Flowers 2006, p. 81.
- All but two of the Colossus computers, which were taken to GCHQ, were dismantled in 1945, and the whole project was kept strictly secret until the 1970s. Thus Colossus did not feature in many early descriptions of the development of electronic computers.Gannon 2007, p. 431
- Roberts 2009.
- Small 1944, p. 1.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, p. 6.
- Gannon 2007, pp. 150, 151.
- Good 1993, p. 153.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, (f) Motors p. 7.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, (g) Limitations p. 8.
- Churchhouse 2002, pp. 158, 159.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11C Wheel patterns, pp. 11, 12.
- This statement is an over-simplification. The real constraint is more complex, that ab=½. For further details see: Good, Michie & Timms 1945, p. 17 in 1 Introduction: 12 Cryptographic Aspects, 12A The Problem, (d) Early methods and Good, Michie & Timms 1945, p. 306 in 42 Early Hand Methods: 42B Machine breaking for March 1942, (e) Value of a and b. Indeed, this weakness was one of the two factors that led to the system being diagnosed.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11E The Tunny Network, (b) Wheel-breaking and Setting, p. 15.
- Hayward 1993, p. 176.
- In more recent terminology, each impulse would be termed a "bit" with a mark being binary 1 and a space being binary 0. Punched paper tape had a hole for a mark and no hole for a space.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11A Fish Machines, (a) The Teleprinter Alphabet, p. 3.
- Roberts 2006, p. 256.
- Good, Michie & Timms 1945, 14 Organisation, 14A Expansion and growth, (a) General position p. 28.
- Intelligence work at secret sites revealed for the first time, GCHQ, 1 November 2019, retrieved 9 July 2020CS1 maint: date and year (link)
- Good, Michie & Timms 1945, 3. Organisation: 33 Knockholt, 33A Ordering tapes, p. 281.
- Bowler, Eileen Eveline (9 November 2005), WW2 People's War, An Archive of World War Two Memories: Listening to the Enemy Radio, BBC London CSV Action Desk
- Gannon 2007, p. 333.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, (i) Functional Summary, p. 10.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11A Fish Machines, (c) The German Ciphered Teleprinter, p. 6.
- Churchhouse 2002, p. 24.
- Copeland 2006, p. 68.
- Copeland 2006, p. 48.
- Edgerley 2006, pp. 273, 274.
- Initially QSN (see Good, Michie & Timms 1945, p. 320 in 44 Early Hand statistical Methods: 44A Introduction of the QEP (QSN) System).
- Copeland 2006, pp. 44–47.
- Good, Michie & Timms 1945, 1 Introduction: 12 Cryptographic Aspects, 12A The Problem, (a) Formulae and Notation, p. 16.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, (e) Psi-key, p. 7.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11C Wheel Patterns, (b) Differenced and Undifferenced Wheels, p. 11.
- Sale, Tony, The Lorenz Cipher and how Bletchley Park broke it, retrieved 21 October 2010
- Good, Michie & Timms 1945, 12 Cryptographic Aspects: 12A The Problem, (c) Weaknesses of Tunny, p. 16.
- Tutte 2006, p. 353.
- Copeland 2010.
- Tutte 1998, p. 4.
- Tutte 2006, p. 356.
- Tutte 2006, p. 357.
- O'Connor, J J; Robertson, E F (2003), MacTutor Biography: William Thomas Tutte, University of St Andrews, retrieved 28 April 2013
- Tutte 2006, pp. 359, 360.
- Copeland 2006, p. 380.
- Good, Michie & Timms 1945, 4 Early Methods and History: 43 Testery Methods 1942-1944, 43B Turingery, p. 313.
- Copeland 2012, p. 96.
- Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11C Wheel patterns, (b) Differenced and Undifferenced Wheels p. 11.
- Small 1944, p. 2 refers to the de-chi as being "pseudo plain"
- Tutte 2006, p. 365.
- Singh, Simon, The Black Chamber, retrieved 28 April 2012
- Newman c. 1944 p. 387
- Carter 2008, p. 14.
- The five impulses or bits of the coded characters are sometimes referred to as five levels.
- Copeland 2006, p. 385 which reproduces a 3 cage from the General Report on Tunny
- Roberts 2009, 34 minutes in.
- Roberts 2006, p. 250.
- Unlike a full depth, when all twelve letters of the indicator were the same, a partial depth occurred when one or two of the indicator letters differed.
- Hayward 1993, pp. 175–192.
- Hayward 2006, p. 291.
- Currie 2006, pp. 265–266.
- Copeland 2006, p. 162 quoting Dorothy Du Boisson.
- Hayward 2006, p. 292.
- Good, Michie & Timms 1945, 51 Introductory: 56. Copying Machines, 56K The (Newmanry) Tunny Machine, pp. 376-378.
- Small 1944, p. 105.
- Good, Michie & Timms 1945, 15 SomeHistorical Notes: 15A. First Stages in Machine Development, p. 33.
- Good, Michie & Timms 1945, 31 Mr Newnam's Section: 31A, Growth, p. 276.
- Good 2006, p. 215.
- The Double-Delta Attack, retrieved 27 June 2018
- Good, Michie & Timms 1945, 44 Hand Statistical Methods: Setting - Statistical pp. 321–322.
- Budiansky 2006, pp. 58–59.
- For this reason Tutte's 1 + 2 method is sometimes called the "double delta" method.
- Tutte 2006, p. 364.
- Carter 2008, pp. 16-17.
- Bletchley Park National Code Centre: November 1943, retrieved 21 November 2012
- Good, Michie & Timms 1945, 15 Some Historical Notes: 15A. First Stages in Machine Development, (c) Heath Robinson p. 33.
- Copeland 2006, p. 65.
- Good, Michie & Timms 1945, 37 Machine Setting Organisation: (b) Robinsons and Colossi p. 290.
- Good, Michie & Timms 1945, 52 Development of Robinson and Colossus: (b) Heath Robinson p. 328.
- Fensom 2006, pp. 300–301.
- Flowers 2006, p. 80.
- Flowers 1983, pp. 245-252.
- Good & Michie 1992.
- Flowers 1983, p. 247.
- Good, Michie & Timms 1945, 13 Machines: 13A Explanation of the Categories, (b) Copying Machines p. 25 and 13C Copying Machines p. 27.
- Good, Michie & Timms 1945, 56 Copying Machines pp. 367–379.
- Good, Michie & Timms 1945, 53 Colossus: 53A Introduction, p. 333.
- Hayward 2006, pp. 291–292.
- Michie 2006, p. 236.
- Fensom 2006, pp. 301–302.
- Good, Michie & Timms 1945, pp. 326 in 51 Introductory: (e) Electronic counters etc.
- Small 1944, p. 107.
- Small 1944, pp. 23, 105.
- Small 1944, p. 9.
- Small 1944, p. 19.
- Small 1944, p. 8.
- Small 1944, p. 7.
- Good, Michie & Timms 1945, 23 Machine Setting: 23B The Choice of Runs, pp. 79,80.
- Good 2006, p. 218.
- Small 1944, p. 20.
- Small 1944, p. 15.
- Adapted from Small 1944, p. 5
Bibliography
- BBC Timewatch (2011), Code Breakers: Bletchley Park's lost Heroes (video)
- Budiansky, Stephen (2006), Colossus, Codebreaking, and the Digital Age in Copeland 2006, pp. 52–63
- Carter, Frank (2008), Codebreaking with the Colossus Computer, Bletchley Park Reports, 1 (New ed.), Bletchley Park Trust, ISBN 978-1-906723-00-2
- Churchhouse, Robert (2002), Codes and Ciphers: Julius Caesar, the Enigma and the Internet, Cambridge: Cambridge University Press, ISBN 978-0-521-00890-7
- Copeland, B. Jack, ed. (2006), Colossus: The Secrets of Bletchley Park's Codebreaking Computers, Oxford: Oxford University Press, ISBN 978-0-19-284055-4
- Copeland, B. Jack (2010), "Colossus: Breaking the German 'Tunny' Code at Bletchley Park. An Illustrated History", The Rutherford Journal, 3
- Copeland, B. Jack (2012), Turing: Pioneer of the Information Age, Oxford: Oxford University Press, ISBN 978-0-19-963979-3
- Currie, Helen (2006), An ATS girl in the Testery in Copeland 2006, pp. 264–268
- Edgerley, Peter (2006), The Testery and the Breaking of Fish in Copeland 2006, pp. 269–277
- Erskine, Ralph; Smith, Michael, eds. (2011) [2001], The Bletchley Park Codebreakers, Biteback Publishing Ltd, ISBN 978-1-84954-078-0 Updated and extended version of Action This Day: From Breaking of the Enigma Code to the Birth of the Modern Computer Bantam Press 2001
- Fensom, Harry (2006), How Colossus was built and Operated in Copeland 2006, pp. 297–304
- Flowers, Thomas H. (1983), "The Design of Colossus", Annals of the History of Computing, 5 (3): 239–252, doi:10.1109/MAHC.1983.10079, S2CID 39816473
- Flowers, Thomas H. (2006), D-Day at Bletchley and Colossus in Copeland 2006, pp. 78–83, 91–100
- Gannon, Paul (2007) [2006], Colossus: Bletchley Park's Greatest Secret, Atlantic Books, ISBN 978-1-84354-331-2
- Good, Jack; Michie, Donald; Timms, Geoffrey (1945), General Report on Tunny: With Emphasis on Statistical Methods, UK Public Record Office HW 25/4 and HW 25/5, archived from the original on 17 September 2010, retrieved 15 September 2010 That version is a facsimile copy, but there is a transcript of much of this document in '.pdf' format at: Sale, Tony (2001), Part of the "General Report on Tunny", the Newmanry History, formatted by Tony Sale (PDF), retrieved 20 September 2010, and a web transcript of Part 1 at: Ellsbury, Graham, General Report on Tunny With Emphasis on Statistical Methods, retrieved 3 November 2010
- Good, Jack; Michie, Donald (1992), I J Good and Donald Michie in conversation with David Kahn and Karen Frrankel, Computer History Museum (published 22 June 2012), retrieved 19 April 2013
- Good, Jack (1993), Enigma and Fish in Hinsley & Stripp 1993, pp. 149–166
- Good, Jack (2006), From Hut 8 to the Newmanry in Copeland 2006, pp. 204–222
- Government Code and Cypher School (1944), The Bletchley Park 1944 Cryptographic Dictionary formatted by Tony Sale (PDF), retrieved 7 October 2010
- Hayward, Gil (1993), Operation Tunny in Hinsley & Stripp 1993, pp. 175–192
- Hayward, Gil (2006), The British Tunny Machine in Copeland 2006, pp. 291–296
- Hinsley, F.H.; Stripp, Alan, eds. (1993) [1992], Codebreakers: The inside story of Bletchley Park, Oxford: Oxford University Press, ISBN 978-0-19-280132-6
- Hinsley, F.H. (1993), Introduction: The influence of Ultra in the Second World War in Hinsley & Stripp 1993, pp. 1–13
- McKay, Sinclair (2010), The Secret Life of Bletchley Park: The WWII Codebreaking Centre and the men and women who worked there, London: Aurum Press, ISBN 978-1-84513-539-3
- Michie, Donald (2006), Codebreaking and Colossus in Copeland 2006, pp. 223–246
- Newman, Max (c. 1944), Appendix 7: Delta-chi Method in Copeland 2006, pp. 386–390
- Roberts, Jerry (2006), "Major Tester's Section", Colossus: The Secrets of Bletchley Park's Codebreaking Computers in Copeland 2006, pp. 249–259
- Roberts, Jerry (2009), My Top-Secret Codebreaking During World War II: The Last British Survivor of Bletchley Park's Testery (iTunes U) (video), University College London
- Small, Albert W. (December 1944), The Special Fish Report, The American National Archive (NARA) College Campus Washington, retrieved 7 March 2013
- Tutte, William T. (2006), Appendix 4: My Work at Bletchley Park in Copeland 2006, pp. 352–369
- Tutte, W. T. (19 June 1998), Fish and I (PDF), retrieved 7 April 2012 Transcript of a lecture given by Prof. Tutte at the University of Waterloo
- Weierud, Frode (2006), Bletchley Park's Sturgeon—The Fish That Laid No Eggs in Copeland 2006, pp. 307–327
- Wylie, Shaun (2001), Breaking Tunny and the birth of Colossus in Erskine & Smith 2011, pp. 283–304
