Rainbow Series
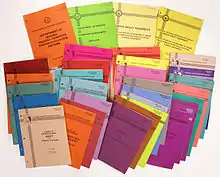
The Rainbow Series (sometimes known as the Rainbow Books) is a series of computer security standards and guidelines published by the United States government in the 1980s and 1990s. They were originally published by the U.S. Department of Defense Computer Security Center, and then by the National Computer Security Center.
Objective
These standards describe a process of evaluation for trusted systems. In some cases, U.S. government entities (as well as private firms) would require formal validation of computer technology using this process as part of their procurement criteria. Many of these standards have influenced, and have been superseded by, the Common Criteria.
The books have nicknames based on the color of its cover. For example, the Trusted Computer System Evaluation Criteria was referred to as "The Orange Book."[1] In the book entitled Applied Cryptography, security expert Bruce Schneier states of NCSC-TG-021 that he "can't even begin to describe the color of [the] cover" and that some of the books in this series have "hideously colored covers." He then goes on to describe how to receive a copy of them, saying "Don't tell them I sent you."[2]
Most significant Rainbow Series books
| Document | Title | Date | Color | |
|---|---|---|---|---|
| 5200.28-STD | DoD Trusted Computer System Evaluation Criteria | August 15, 1983 | Orange | |
| CSC-STD-002-85 | DoD Password Management Guideline | April 12, 1985 | Green | |
| CSC-STD-003-85 | Guidance for applying TCSEC in Specific Environments | June 25, 1985 | Light Yellow | |
| CSC-STD-004-85 | Technical Rationale Behind CSC-STD-003-85: Computer Security Requirements | June 25, 1985 | Yellow | |
| NCSC-TG-001 | A Guide to Understanding Audit in Trusted Systems | June 1, 1988 | Tan | |
| NCSC-TG-002 | Trusted Product Security Evaluation Program | June 22, 1990 | Bright Blue | |
| NCSC-TG-003 | Discretionary Access Control in Trusted Systems | September 30, 1987 | Neon Orange | |
| NCSC-TG-004 | Glossary of Computer Security Terms | October 21, 1988 | Teal Green | |
| NCSC-TG-005 | Trusted Network Interpretation | July 31, 1987 | Red | |
| NCSC-TG-006 | Configuration Management in Trusted Systems | March 28, 1988 | Amber | |
| NCSC-TG-007 | A Guide to Understanding Design Documentation in Trusted Systems | October 6, 1988 | Burgundy | |
| NCSC-TG-008 | A Guide to Understanding Trusted Distribution in Trusted Systems | December 15, 1988 | Dark Lavender | |
| NCSC-TG-009 | Computer Security Subsystem Interpretation of the TCSEC | September 16, 1988 | Venice Blue | |
| NCSC-TG-010 | A Guide to Understanding Security Modeling in Trusted Systems | October 1992 | Aqua | |
| NCSC-TG-011 | Trusted Network Interpretation Environments Guideline (TNI) | August 1, 1990 | Red | |
| NCSC-TG-013 | RAMP Program Document | 1989 | Pink | |
| NCSC-TG-013 V2 | RAMP Program Document version 2 | March 1, 1995 | Pink | |
| NCSC-TG-014 | Guidelines for Formal Verification Systems | April 1, 1989 | Purple | |
| NCSC-TG-015 | Guide to Understanding Trusted Facility Management | October 18, 1989 | Brown | |
| NCSC-TG-016 | Guidelines for Writing Trusted Facility Manuals | October 1992 | Yellow-Green | |
| NCSC-TG-017 | Identification and Authentication in Trusted Systems | September 1991 | Light Blue | |
| NCSC-TG-018 | Object Reuse in Trusted Systems | July 1992 | Light Blue | |
| NCSC-TG-019 | Trusted Product Evaluation Questionnaire | May 2, 1992 | Blue | |
| NCSC-TG-020 | Trusted UNIX Working Group (TRUSIX) Rationale for Selecting Access Control List Features for the UNIX System | July 7, 1989 | Silver | |
| NCSC-TG-020-A | Trusted UNIX Working Group (TRUSIX) Rationale for Selecting Access Control List Features for the UNIX (R) System | August 18, 1989 | Grey Silver | |
| NCSC-TG-021 | Trusted Database Management System Interpretation of the TCSEC (TDI) | April 1991 | Purple | |
| NCSC-TG-022 | Trusted Recovery in Trusted Systems | December 30, 1991 | Yellow | |
| NCSC-TG-023 | Security Testing and Test Documentation in Trusted Systems | July 1993 | Bright Orange | |
| NCSC-TG-024 Vol. 1/4 | Procurement of Trusted Systems: An Introduction to Procurement Initiators on Computer Security Requirements | December 1992 | Purple | |
| NCSC-TG-024 Vol. 2/4 | Procurement of Trusted Systems: Language for RFP Specifications and Statements of Work | June 30, 1993 | Purple | |
| NCSC-TG-024 Vol. 3/4 | Procurement of Trusted Systems: Computer Security Contract Data Requirements List and Data Item Description | February 28, 1994 | Purple | |
| NCSC-TG-024 Vol. 4/4 | Procurement of Trusted Systems: How to Evaluate a Bidder's Proposal Document | Publication TBA | Purple | |
| NCSC-TG-025 | Guide to Understanding Data Remanence in Automated Information Systems. | September 1991 | Forest Green | |
| NCSC-TG-026 | Writing the Security Features User's Guide for Trusted Systems | September 1991 | Hot Peach | |
| NCSC-TG-027 | Information System Security Officer Responsibilities for Automated Information Systems | May 1992 | Turquoise | |
| NCSC-TG-028 | Assessing Controlled Access Protection | May 25, 1992 | Violet | |
| NCSC-TG-029 | Certification and Accreditation Concepts | January 1994 | Blue | |
| NCSC-TG-030 | Covert Channel Analysis of Trusted Systems | November 1993 | Light Pink | |
References
- Steve Lipner, "The Birth and Death of the Orange Book" IEEE Annals of the History of Computing 37 no. 2 (2015): 19-31 at DOI
- Schneier, Bruce (1996), Applied Cryptography (2nd ed.), New York, NY: John Wiley and Sons, ISBN 978-0-471-11709-4
External links
- Rainbow Series from Federation of American Scientists, with more explanation
- Rainbow Series from Archive of Information Assurance