The Fourth Protocol (video game)
The Fourth Protocol is an interactive fiction video game based on Frederick Forsyth's 1984 spy novel The Fourth Protocol. The game was released in 1985 by Hutchinson Computer Publishing, a subsidiary of the publishing house Hutchinson. It was designed by John Lambshead and Gordon Paterson, and programmed by Ben Notarianni, Rupert Bowater and Paul Norris of the Electronic Pencil Company.[1] The game was released for the ZX Spectrum in July 1985, with the Commodore 64 release following one month later, and the Amstrad CPC conversion in 1986.
| The Fourth Protocol | |
|---|---|
 European cover art | |
| Developer(s) | Electronic Pencil Company |
| Publisher(s) |
|
| Designer(s) | John Lambshead Gordon Paterson |
| Composer(s) | David Dunn |
| Platform(s) | ZX Spectrum, Commodore 64, Amstrad CPC, IBM PC |
| Release | 1985 |
| Mode(s) | Single-player |
The game is split into three parts, and large sections of the programming were outsourced to others: Andrew Glaister (program conversion Spectrum, parts one and two), Dave Jones (programming Spectrum, part three), Ray Owen (graphics Spectrum, part three) and John Gibbons (programming C64, part three). The IBM PC version was developed for the Electronic Pencil company, by a developer named Brian Mallett. The PC version was written in 8086 assembler and used CGA graphics in 4 colour mode. The PC version was ported from the Z80 and 6502 versions. The PC version did not use DOS but booted up from its own floppy disk.
The game was published in the US by Bantam Software.
Gameplay
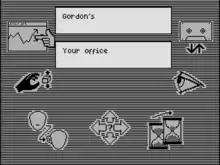
The game comprises three sections: "The NATO Documents", "The Bomb" and "The SAS Assault". In order to progress to the last two sections, the player must solve riddles based on the current and any previous sections. Macintosh-like icons are used to assign watchers and navigate until text-based interaction becomes available in the third section.
The NATO documents

The scene is Preston's office. The player takes the role of John Preston, the new head of Section C1(A). Somewhere in England, a burglar steals the famous Glen Diamonds, but he also finds some secret NATO documents. He alerts the MoD by sending them the documents anonymously. The Paragon Committee decides that John Preston's most important task is to find out who is leaking secrets, to whom they are being leaked and why. Other events occur along the way which also demand his attention.
The Cencom icon offers access to Preston's personal files where the player can store information throughout the first part of the game. The Assessment icon gives the player an idea of their progress, telling the player how much of the first stage they have solved and their current rating at MI5. Using surveillance the player can assign 'watchers' to targets; these are informants who provide valuable information, in addition to memos and reports, which will be brought to the player's attention via the sitreps icon. The calendar icon lets the player know how much time has passed. The telephone icon allows the player to accept calls or call out. It is also possible to save and restore the game at any point.
The bomb
From the clues in the first section, the player should have an idea about the plot and who could be responsible. This section is similar in gameplay to the first section, but the player is now in the field, on the trail of the nuclear device which has been smuggled into the country.
This section adds additional icons to control movement, along with a manipulate icon to take, drop and use objects. The player is able to look around and examine objects. The communicate icon allows the player to talk to others, via the phone if needed.
SAS assault
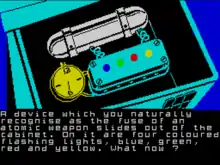
In this section, the player has discovered the location of the bomb. Using the information the player has gathered in the previous two parts, they must work out how to defuse the device. This part of the trilogy requires text input and plays differently depending on the version of the game.
External links
- The Fourth Protocol at SpectrumComputing.co.uk
- The Fourth Protocol at Gamebase 64
- Images of the package and manual