NESTOR (encryption)
NESTOR was a family of compatible, tactical, wideband secure voice systems developed by the U.S. National Security Agency and widely deployed during the Vietnam War through the late Cold War period of the 1980s. NESTOR consists of three systems. The KY-8 was used in vehicular and afloat applications; the KY-28 was the airborne version: and the KY-38 was the portable or man-pack model. About 30,000 NESTOR equipments were produced prior to their replacement by the VINSON secure voice family.[1]:Vol I, p.79

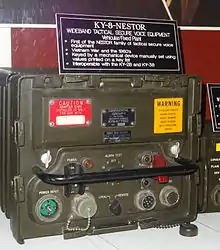



Keying was accomplished by setting each switch in a matrix of switches to one of several positions. This was done using a separate mechanical key loader (KYK-28) that had a matching matrix of pins that could be set to different heights as instructed by a key list. The key loader was pushed into a matrix of holes, one hole for each switch. The loader also had two larger index pins that also cocked a spring that would return each switch to their initial position when the door covering the hole matrix was reopened, zeroizing the equipment.[2][3]
Vietnam War experience
NSA gave high priority to deploying NESTOR systems in Vietnam. Equipment was issued to field units in Vietnam beginning in 1965 with the KY-8 for stationary or vehicular use; the KY-8 was fully distributed by the third quarter of the fiscal year 1968. The KY-28 was issued for use in aircraft beginning in 1967, as was the KY-38 for man-pack or mobile use. The KY-38 was fully distributed in 1968.[4] NESTOR was successfully used in some situations, but the overall experience was not good. NSA estimates that only about one in ten units were actually used. A variety of problems contributed to this rejection:[1]:Vol II, p.43ff
- Voice quality was poor
- NESTOR reduced the range of radios by 10%. While this did not happen in tests with carefully tuned radios, it did in the field.
- The roughly 600 millisecond delay before NESTOR enabled radios would synchronize after each "push to talk" was intolerable to pilots in air to air combat.
- While the KY-28 was easily incorporated in bomber (e.g., B-52), attack (e.g., AC-119, AC-130), large reconnaissance (e.g., P-3, RC-135) and command and control (e.g., EC-121, E-1, E-2) aircraft during its initial introduction, finding room for the KY-28 in fighter aircraft was difficult. The Navy improvised successfully, for example tucking KY-28s into the nose wheel well of F-4 Phantoms, while the Air Force initiated a formal modification program that took years to complete.
- The ground version, KY-8 wouldn't work in the high temperatures common in the country, leading to jury-rigged cooling solutions, like wrapping units in wet burlap, or drilling unauthorized holes in the case.
- The human portable version, KY-38, while a marvel of miniaturization for the time, was still heavy. The KY-38 plus AN/PRC-77 radio and spare batteries weighed about 54 pounds (24.5 kg). Experiments with having two Marines carry the separate units with a cable between worked poorly in the jungle. Many units decided that more ammunition was a better use of carrying capacity.
- Lack of cables to connect NESTOR equipment to radios proved to be a major problem that was never fully solved due to lack of coordination between three separate organizations responsible for procuring the encryption systems, radios and cables. One large batch of replacement cables was lost in a cargo plane crash.[2]
- NSA doctrine called for limiting the number of radios (250 at first, later 400) on a network with a common key, to limit the risk of key compromise. This meant units could sometimes not communicate with other units in the field in a highly mobile war. NSA eventually had to relax this restriction for air ground communication since aircraft could go anywhere. Also ground forces used FM radios, while aircraft used AM, limiting secure cross communication to units equipped with compatible NESTOR-equipped radios.
- Some commanders were concerned about carrying the classified-Confidential NESTOR units into combat, for fear that their military careers might be damaged by the loss of classified material. Some 1001 NESTOR units were lost during the war, mostly in downed aircraft and there was no record of anyone being disciplined for losing a unit "while trying to fight a war with it." Surveys suggested this issue was not a major factor, with fear that captured units might be used by the enemy being a greater concern. But it led to an ongoing controversy within NSA about the desirability of fielding cryptographic equipment that was not classified.
- NSA cryptoperiod doctrine called for keys to be changed every 24 hours. Initially these key changes took place at midnight, local time, taking all secure radios out of service for several minutes. This timing proved particularly inopportune because most contacts with opposing forces took place at night. The key-change time was later changed to 0600 to avoid this problem.[4]
While many in the U.S. military believed that the Viet Cong and NVA would not be able to exploit unsecure communications, interrogation of captured communication intelligence units showed they were able to understand the American's jargon and informal codes in realtime and were often able to warn their side of impending U.S. actions.[1]:Vol II, pp. 4, 10
See also
References
- A History of U.S. Communications Security; the David G. Boak Lectures, National Security Agency (NSA), Volumes I, 1973, Volumes II 1981, partially released 2008, additional portions declassified October 14, 2015
- "KY-38 Voice Security Unit". www.prc68.com.
- "KY28 Cryptosystem". www.jproc.ca.
- Vietnam Studies—Division-Level Communications 1962-1973, Lieutenant General Charles R. Myer, U.S. Department of the Army, 1982, Chapter 8
