Virtual private network
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. Applications running across a VPN may therefore benefit from the functionality, security, and management of the private network. Encryption is a requirement of a VPN[1].

VPN technology was developed to provide access to corporate applications and resources to remote users, mobile users, and to branch offices. For security, the private network connection may be established using an encrypted layered tunneling protocol, and users may be required to pass various authentication methods to gain access to the VPN. In other applications, Internet users may secure their connections with a VPN to circumvent geo-blocking and censorship or to connect to proxy servers to hide their IP address from the target server. Some websites, however, block access to known IP addresses used by VPNs to prevent the circumvention of their geo-restrictions,[2] and many VPN providers have been developing strategies to get around these blockades.
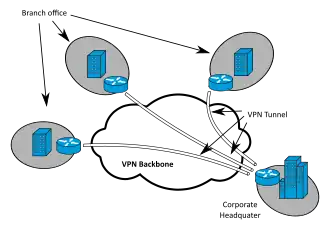
A VPN is created by establishing a virtual point-to-point connection through the use of dedicated circuits or with tunneling protocols over existing networks.[2] A VPN available from the public Internet can provide some of the benefits of a wide area network (WAN). From a user perspective, the resources available within the private network can be accessed remotely.[3]
Types
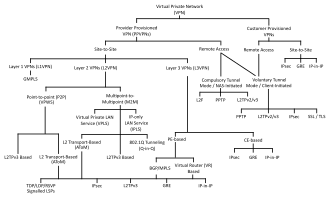
Three broad categories of VPNs exist, namely remote access, intranet-based site-to-site, and extranet-based site-to-site.[4] While individual users most frequently interact with remote access VPNs, businesses make use of site-to-site VPNs more often.[4]
Early data networks allowed VPN-style connections to remote sites through dial-up modem or through leased line connections utilizing X.25, Frame Relay and Asynchronous Transfer Mode (ATM) virtual circuits provided through networks owned and operated by telecommunication carriers. These networks are not considered true VPNs because they passively secure the data being transmitted by the creation of logical data streams.[5] They have been replaced by VPNs based on IP and IP/Multi-protocol Label Switching (MPLS) Networks, due to significant cost-reductions and increased bandwidth[6] provided by new technologies such as digital subscriber line (DSL)[7] and fiber-optic networks.
VPNs can be characterized as host-to-network or remote access by connecting a single computer to a network or as site-to-site for connecting two networks. In a corporate setting, remote-access VPNs allow employees to access the company's intranet from outside the office. Site-to-site VPNs allow collaborators in geographically disparate offices to share the same virtual network. A VPN can also be used to interconnect two similar networks over a dissimilar intermediate network, such as two IPv6 networks connected over an IPv4 network.[8]
VPN systems may be classified by:
- the tunneling protocol used to tunnel the traffic
- the tunnel's termination point location, e.g., on the customer edge or network-provider edge
- the type of topology of connections, such as site-to-site or network-to-network
- the levels of security provided
- the OSI layer they present to the connecting network, such as Layer 2 circuits or Layer 3 network connectivity
- the number of simultaneous connections
Security mechanisms
VPNs cannot make online connections completely anonymous, but they can usually increase privacy and security. To prevent disclosure of private information, VPNs typically allow only authenticated remote access using tunneling protocols and encryption techniques.
The VPN security model provides:
- confidentiality such that even if the network traffic is sniffed at the packet level (see network sniffer and deep packet inspection), an attacker would see only encrypted data
- sender authentication to prevent unauthorized users from accessing the VPN
- message integrity to detect any instances of tampering with transmitted messages.
Secure VPN protocols include the following:
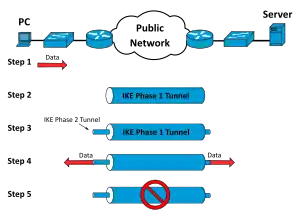
- Internet Protocol Security (IPsec) was initially developed by the Internet Engineering Task Force (IETF) for IPv6, which was required in all standards-compliant implementations of IPv6 before RFC 6434 made it only a recommendation.[9] This standards-based security protocol is also widely used with IPv4 and the Layer 2 Tunneling Protocol. Its design meets most security goals: availability, integrity, and confidentiality. IPsec uses encryption, encapsulating an IP packet inside an IPsec packet. De-encapsulation happens at the end of the tunnel, where the original IP packet is decrypted and forwarded to its intended destination.
- Transport Layer Security (SSL/TLS) can tunnel an entire network's traffic (as it does in the OpenVPN project and SoftEther VPN project[10]) or secure an individual connection. A number of vendors provide remote-access VPN capabilities through SSL. An SSL VPN can connect from locations where IPsec runs into trouble with Network Address Translation and firewall rules.
- Datagram Transport Layer Security (DTLS) – used in Cisco AnyConnect VPN and in OpenConnect VPN[11] to solve the issues SSL/TLS has with tunneling over TCP (tunneling TCP over TCP can lead to big delays and connection aborts[12]).
- Microsoft Point-to-Point Encryption (MPPE) works with the Point-to-Point Tunneling Protocol and in several compatible implementations on other platforms.
- Microsoft Secure Socket Tunneling Protocol (SSTP) tunnels Point-to-Point Protocol (PPP) or Layer 2 Tunneling Protocol traffic through an SSL/TLS channel (SSTP was introduced in Windows Server 2008 and in Windows Vista Service Pack 1).
- Multi Path Virtual Private Network (MPVPN). Ragula Systems Development Company owns the registered trademark "MPVPN".[13]
- Secure Shell (SSH) VPN – OpenSSH offers VPN tunneling (distinct from port forwarding) to secure remote connections to a network or to inter-network links. OpenSSH server provides a limited number of concurrent tunnels. The VPN feature itself does not support personal authentication.[14][15][16]
- WireGuard is a protocol. In 2020, WireGuard support was added to both the Linux[17] and Android[18] kernels, opening it up to adoption by VPN providers. By default, WireGuard utilizes Curve25519 for key exchange and ChaCha20 for encryption, but also includes the ability to pre-share a symmetric key between the client and server.[19] Almost all commercial VPNs adopted this protocol as the default one.
Authentication
Tunnel endpoints must be authenticated before secure VPN tunnels can be established. User-created remote-access VPNs may use passwords, biometrics, two-factor authentication or other cryptographic methods. Network-to-network tunnels often use passwords or digital certificates. They permanently store the key to allow the tunnel to establish automatically, without intervention from the administrator
Routing
Tunneling protocols can operate in a point-to-point network topology that would theoretically not be considered a VPN because a VPN by definition is expected to support arbitrary and changing sets of network nodes. But since most router implementations support a software-defined tunnel interface, customer-provisioned VPNs often are simply defined tunnels running conventional routing protocols.
Provider-provisioned VPN building-blocks
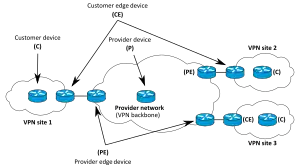
Depending on whether a provider-provisioned VPN (PPVPN) operates in layer 2 or layer 3, the building blocks described below may be L2 only, L3 only, or a combination of both. Multi-protocol label switching (MPLS) functionality blurs the L2-L3 identity.{{[20]}}
RFC 4026 generalized the following terms to cover L2 MPLS VPNs and L3 (BGP) VPNs, but they were introduced in RFC 2547.[21][22]
- Customer (C) devices
A device that is within a customer's network and not directly connected to the service provider's network. C devices are not aware of the VPN.
- Customer Edge device (CE)
A device at the edge of the customer's network which provides access to the PPVPN. Sometimes it is just a demarcation point between provider and customer responsibility. Other providers allow customers to configure it.
- Provider edge device (PE)
A device, or set of devices, at the edge of the provider network which connects to customer networks through CE devices and presents the provider's view of the customer site. PEs are aware of the VPNs that connect through them, and maintain VPN state.
- Provider device (P)
A device that operates inside the provider's core network and does not directly interface to any customer endpoint. It might, for example, provide routing for many provider-operated tunnels that belong to different customers' PPVPNs. While the P device is a key part of implementing PPVPNs, it is not itself VPN-aware and does not maintain VPN state. Its principal role is allowing the service provider to scale its PPVPN offerings, for example, by acting as an aggregation point for multiple PEs. P-to-P connections, in such a role, often are high-capacity optical links between major locations of providers.
User-visible PPVPN services
OSI Layer 2 services
- Virtual LAN
Virtual LAN (VLAN) is a Layer 2 technique that allow for the coexistence of multiple local area network (LAN) broadcast domains interconnected via trunks using the IEEE 802.1Q trunking protocol. Other trunking protocols have been used but have become obsolete, including Inter-Switch Link (ISL), IEEE 802.10 (originally a security protocol but a subset was introduced for trunking), and ATM LAN Emulation (LANE).
- Virtual private LAN service (VPLS)
Developed by Institute of Electrical and Electronics Engineers, Virtual LANs (VLANs) allow multiple tagged LANs to share common trunking. VLANs frequently comprise only customer-owned facilities. Whereas VPLS as described in the above section (OSI Layer 1 services) supports emulation of both point-to-point and point-to-multipoint topologies, the method discussed here extends Layer 2 technologies such as 802.1d and 802.1q LAN trunking to run over transports such as Metro Ethernet.
As used in this context, a VPLS is a Layer 2 PPVPN, emulating the full functionality of a traditional LAN. From a user standpoint, a VPLS makes it possible to interconnect several LAN segments over a packet-switched, or optical, provider core, a core transparent to the user, making the remote LAN segments behave as one single LAN.[23]
In a VPLS, the provider network emulates a learning bridge, which optionally may include VLAN service.
- Pseudo wire (PW)
PW is similar to VPLS, but it can provide different L2 protocols at both ends. Typically, its interface is a WAN protocol such as Asynchronous Transfer Mode or Frame Relay. In contrast, when aiming to provide the appearance of a LAN contiguous between two or more locations, the Virtual Private LAN service or IPLS would be appropriate.
- Ethernet over IP tunneling
EtherIP (RFC 3378)[24] is an Ethernet over IP tunneling protocol specification. EtherIP has only packet encapsulation mechanism. It has no confidentiality nor message integrity protection. EtherIP was introduced in the FreeBSD network stack[25] and the SoftEther VPN[26] server program.
- IP-only LAN-like service (IPLS)
A subset of VPLS, the CE devices must have Layer 3 capabilities; the IPLS presents packets rather than frames. It may support IPv4 or IPv6.
OSI Layer 3 PPVPN architectures
This section discusses the main architectures for PPVPNs, one where the PE disambiguates duplicate addresses in a single routing instance, and the other, virtual router, in which the PE contains a virtual router instance per VPN. The former approach, and its variants, have gained the most attention.
One of the challenges of PPVPNs involves different customers using the same address space, especially the IPv4 private address space.[27] The provider must be able to disambiguate overlapping addresses in the multiple customers' PPVPNs.
- BGP/MPLS PPVPN
In the method defined by RFC 2547, BGP extensions advertise routes in the IPv4 VPN address family, which are of the form of 12-byte strings, beginning with an 8-byte route distinguisher (RD) and ending with a 4-byte IPv4 address. RDs disambiguate otherwise duplicate addresses in the same PE.
PEs understand the topology of each VPN, which are interconnected with MPLS tunnels either directly or via P routers. In MPLS terminology, the P routers are Label Switch Routers without awareness of VPNs.
- Virtual router PPVPN
The virtual router architecture,[28][29] as opposed to BGP/MPLS techniques, requires no modification to existing routing protocols such as BGP. By the provisioning of logically independent routing domains, the customer operating a VPN is completely responsible for the address space. In the various MPLS tunnels, the different PPVPNs are disambiguated by their label but do not need routing distinguishers.
Unencrypted tunnels
Some virtual networks use tunneling protocols without encryption for protecting the privacy of data. While VPNs often do provide security, an unencrypted overlay network does not neatly fit within the secure or trusted categorization.[30] For example, a tunnel set up between two hosts with Generic Routing Encapsulation (GRE) is a virtual private network but is neither secure nor trusted.[31][32]
Native plaintext tunneling protocols include Layer 2 Tunneling Protocol (L2TP) when it is set up without IPsec and Point-to-Point Tunneling Protocol (PPTP) or Microsoft Point-to-Point Encryption (MPPE).[33]
Trusted delivery networks
Trusted VPNs do not use cryptographic tunneling; instead they rely on the security of a single provider's network to protect the traffic.[34]
- Multi-Protocol Label Switching (MPLS) often overlays VPNs, often with quality-of-service control over a trusted delivery network.
- L2TP[35] which is a standards-based replacement, and a compromise taking the good features from each, for two proprietary VPN protocols: Cisco's Layer 2 Forwarding (L2F)[36] (obsolete as of 2009) and Microsoft's Point-to-Point Tunneling Protocol (PPTP).[37]
From the security standpoint, VPNs either trust the underlying delivery network or must enforce security with mechanisms in the VPN itself. Unless the trusted delivery network runs among physically secure sites only, both trusted and secure models need an authentication mechanism for users to gain access to the VPN.
Types of deployment
VPNs in mobile environments
Users utilize mobile virtual private networks in settings where an endpoint of the VPN is not fixed to a single IP address, but instead roams across various networks such as data networks from cellular carriers or between multiple Wi-Fi access points without dropping the secure VPN session or losing application sessions.[38] Mobile VPNs are widely used in public safety where they give law-enforcement officers access to applications such as computer-assisted dispatch and criminal databases,[39] and in other organizations with similar requirements such as Field service management and healthcare[40].
VPN on routers
With the increasing use of VPNs, many have started deploying VPN connectivity on routers for additional security and encryption of data transmission by using various cryptographic techniques.[41] Home users usually deploy VPNs on their routers to protect devices such as smart TVs or gaming consoles, which are not supported by native VPN clients. Supported devices are not restricted to those capable of running a VPN client.[42]
Many router manufacturers supply routers with built-in VPN clients. Some use open-source firmware such as DD-WRT, OpenWRT and Tomato in order to support additional protocols such as OpenVPN.
Setting up VPN services on a router requires a deep knowledge of network security and careful installation. Minor misconfiguration of VPN connections can leave the network vulnerable. Performance will vary depending on the Internet service provider (ISP).[43]
Networking limitations
A limitation of traditional VPNs is that they are point-to-point connections and do not tend to support broadcast domains; therefore, communication, software, and networking, which are based on layer 2 and broadcast packets, such as NetBIOS used in Windows networking, may not be fully supported as on a local area network. Variants on VPN such as Virtual Private LAN Service (VPLS) and layer 2 tunneling protocols are designed to overcome this limitation.[44]
Tor
It is impossible to hide Tor use from Internet Service Providers (ISP) by using a VPN, since technical analyses have demonstrated this goal to be too difficult to be practical.[45] VPNs are vulnerable to an attack called website traffic fingerprinting.[46]
Both the ISP and a local network administrator can easily check if connections are made to a Tor relay and not a normal web server. The destination server contacted through Tor can learn whether the communication originates from a Tor exit relay by consulting the publicly available list of known exit relays. For example, The Tor Project Bulk Exit List tool could be used for this purpose.[47]
VPN services
A wide variety of (typically commercial) entities provide "VPNs" for all kinds of purposes, but depending on the provider and the application, they often do not create a true "private network" with anything meaningful on the local network. Nonetheless the term is increasingly prevalent. The general public has come to mainly use the term VPN service or just VPN specifically for a commercially marketed product or service that uses a VPN protocol to tunnel the user's internet traffic so an IP address of the service provider's server appears to the public to be the IP address of the user. Depending on the features properly implemented, the user's traffic, location and/or real IP may be hidden from the public, thereby providing the desired internet access features offered, such as Internet censorship circumvention, IP-address masking (not to be confused with anonymity), and geo-unblocking. They tunnel the user's internet traffic securely only between the public internet and the user's device and there is typically no way for a user's devices connected to the same "VPN" to see each other. These VPNs can be based on typical VPN protocols or more camouflaged VPN implementations like SoftEther VPN, but proxy protocols like Shadowsocks are used as well.[48] These VPNs are usually marketed as privacy protection services.
On the client side, a common VPN setup is by design not a conventional VPN, but does typically use the operating system's VPN interfaces to capture a user's data to send through. This include virtual network adapters on computer OSes and specialized "VPN" interfaces on mobile operating systems. A less common alternative is to provide a SOCKS proxy interface.
Users must consider that when the transmitted content is not encrypted before entering a VPN, that data is visible at the receiving endpoint (usually the public VPN provider's site) regardless of whether the VPN tunnel wrapper itself is encrypted for the inter-node transport. The only secure VPN is where the participants have oversight at both ends of the entire data path, or the content is encrypted before it enters the tunnel provider.
As of March 2020 it is estimated that over 30% of Internet users around the world use a commercial VPN, with that number higher in the Middle East, Asia, and Africa.[49]
Legality
China
Unapproved VPNs are illegal in China, as they can be used by the citizens to circumvent the Great Firewall. (VPN refers to any protocol that tunnels traffic out elsewhere, as above.)[50] There have been jail terms and fines imposed on people selling unauthorized VPN service.[51][52] Individuals have also been fined for accessing websites using VPN.[53][54]
The ban does not apply to foreign companies, and domestic government institutions and companies.[55] Chinese government spokespeople, such as Zhao Lijian and Hua Chunying, and editor Hu Xijin from the state-linked Global Times, have official social media accounts on Twitter, a service which is banned in Mainland China.[56]
See also
References
- "What is a VPN?". CISCO. Retrieved 6 February 2021.
- "What is a VPN (Virtual Private Network) and How Does It Work?". SearchNetworking. Retrieved 16 October 2020.
- "Virtual Private Networking: An Overview". Microsoft Technet. 4 September 2001.
- "Different Types of VPNs and When to Use Them (Updated 2020)". vpnMentor. Retrieved 16 October 2020.
- Cisco Systems, et al. Internet working Technologies Handbook, Third Edition. Cisco Press, 2000, p. 232.
- Lewis, Mark. Comparing, Designing. And Deploying VPNs. Cisco Press, 2006, p. 5
- International Engineering Consortium. Digital Subscriber Line 2001. Intl. Engineering Consortium, 2001, p. 40.
- Technet Lab. "IPv6 traffic over VPN connections". Archived from the original on 15 June 2012.
- RFC 6434, "IPv6 Node Requirements", E. Jankiewicz, J. Loughney, T. Narten (December 2011)
- "1. Ultimate Powerful VPN Connectivity". www.softether.org. SoftEther VPN Project.
- "OpenConnect". Retrieved 8 April 2013.
OpenConnect is a client for Cisco's AnyConnect SSL VPN [...] OpenConnect is not officially supported by, or associated in any way with, Cisco Systems. It just happens to interoperate with their equipment.
- "Why TCP Over TCP Is A Bad Idea". sites.inka.de. Retrieved 24 October 2018.
- "Trademark Status & Document Retrieval". tarr.uspto.gov.
- "ssh(1) – OpenBSD manual pages". man.openbsd.org.
- c@cb.vu, Colin Barschel. "Unix Toolbox". cb.vu.
- "SSH_VPN – Community Help Wiki". help.ubuntu.com.
- Salter, Jim (30 March 2020). "WireGuard VPN makes it to 1.0.0—and into the next Linux kernel". Ars Technica. Retrieved 30 June 2020.
- "Diff - 99761f1eac33d14a4b1613ae4b7076f41cb2df94^! - kernel/common - Git at Google". android.googlesource.com. Retrieved 30 June 2020.
- Younglove, R. (December 2000). "Virtual private networks - how they work". Computing & Control Engineering Journal. 11 (6): 260–262. doi:10.1049/cce:20000602. ISSN 0956-3385.
- (PDF) https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst6500/ios/12-2SXF/native/configuration/guide/swcg/pfc3mpls.pdf. Missing or empty
|title=(help) - E. Rosen & Y. Rekhter (March 1999). "BGP/MPLS VPNs". Internet Engineering Task Force (IETF). RFC 2547.
- Lewis, Mark (2006). Comparing, designing, and deploying VPNs (1st print. ed.). Indianapolis, Ind.: Cisco Press. pp. 5–6. ISBN 1587051796.
- Ethernet Bridging (OpenVPN)
- Hollenbeck, Scott; Housley, Russell. "EtherIP: Tunneling Ethernet Frames in IP Datagrams".
- Glyn M Burton: RFC 3378 EtherIP with FreeBSD, 03 February 2011
- net-security.org news: Multi-protocol SoftEther VPN becomes open source, January 2014
- Address Allocation for Private Internets, RFC 1918, Y. Rekhter et al., February 1996
- RFC 2917, A Core MPLS IP VPN Architecture
- RFC 2918, E. Chen (September 2000)
- Yang, Yanyan (2006). "IPsec/VPN security policy correctness and assurance". Journal of High Speed Networks. 15: 275–289. CiteSeerX 10.1.1.94.8561.
- "Overview of Provider Provisioned Virtual Private Networks (PPVPN)". Secure Thoughts. Retrieved 29 August 2016.
- RFC 1702: Generic Routing Encapsulation over IPv4 networks. October 1994.
- IETF (1999), RFC 2661, Layer Two Tunneling Protocol "L2TP"
- Cisco Systems, Inc. (2004). Internetworking Technologies Handbook. Networking Technology Series (4 ed.). Cisco Press. p. 233. ISBN 9781587051197. Retrieved 15 February 2013.
[...] VPNs using dedicated circuits, such as Frame Relay [...] are sometimes called trusted VPNs, because customers trust that the network facilities operated by the service providers will not be compromised.
- Layer Two Tunneling Protocol "L2TP", RFC 2661, W. Townsley et al., August 1999
- IP Based Virtual Private Networks, RFC 2341, A. Valencia et al., May 1998
- Point-to-Point Tunneling Protocol (PPTP), RFC 2637, K. Hamzeh et al., July 1999
- Phifer, Lisa. "Mobile VPN: Closing the Gap", SearchMobileComputing.com, July 16, 2006.
- Willett, Andy. "Solving the Computing Challenges of Mobile Officers", www.officer.com, May, 2006.
- Cheng, Roger. "Lost Connections", The Wall Street Journal, December 11, 2007.
- "Encryption and Security Protocols in a VPN". Retrieved 23 September 2015.
- "VPN". Draytek. Retrieved 19 October 2016.
- "How can incorrectly configuring VPN clients lead to a security breach?". SearchEnterpriseWAN. Retrieved 14 August 2018.
- "Virtual Private Networking: An Overview". 18 November 2019.
- "Hide Tor from your Internet Service Provider". Whonix.
- "Tor plus VPN and VPNSSH Fingerprinting".
- "TorBEL: The Tor Bulk Exit List Tools | Tor Blog". blog.torproject.org. Retrieved 14 October 2020.
- Hodge, Rae. "Proxy vs. VPN: If it's built into your browser, it might not be a true VPN". CNET. Retrieved 21 January 2020.
- Migliano, Simon (17 March 2020). "Global VPN Usage Statistics in 2020". Top10VPN.com. GlobalWebIndex. Retrieved 10 November 2020.
- "Businesses, consumers uncertain ahead of China VPN ban". Reuters. Retrieved 3 April 2018.
- "Man jailed for 5½ years, fined US$76,000 for selling VPN in China". South China Morning Post. 21 December 2017. Retrieved 10 August 2020.
- Cimpanu, Catalin. "Chinese man arrested after making $1.6 million from selling VPN services". ZDNet. Retrieved 10 August 2020.
- "Using a VPN to watch porn gets a man punished in China". South China Morning Post. 30 July 2020. Retrieved 10 August 2020.
- ""翻墙"网民受罚 中国进一步强化网络管控" [Internet User Fined for Scaling Great Firewall - China strengthens Internet Control]. BBC News 中文 (in Chinese). 11 January 2019. Retrieved 10 August 2020.
- Tone, Sixth. "China's VPN Regulations Won't Affect Companies, Official Says". Sixth Tone. Retrieved 10 August 2020.
- Ryan, Fergus. "China's Online Warriors Want More Gates in the Firewall". Foreign Policy. Retrieved 10 August 2020.
Further reading
- Kelly, Sean (August 2001). "Necessity is the mother of VPN invention". Communication News: 26–28. ISSN 0010-3632. Archived from the original on 17 December 2001.