Electronic voting in the United States
Electronic voting in the United States involves several types of machines: touch screens for voters to mark choices, scanners to read paper ballots, scanners to verify signatures on envelopes of absentee ballots, and web servers to display tallies to the public. Aside from voting, there are also computer systems to maintain voter registrations and display these electoral rolls to polling place staff.
 |
|---|
| This article is part of a series on the politics and government of the United States |
|
|
Most election offices handle thousands of ballots, with an average of 17 contests per ballot,[1] so machine-counting can be faster and less expensive than hand-counting.
Voluntary guidelines
The Election Assistance Commission (EAC) is an independent agency of the United States government which developed the 2005 Voluntary Voting System Guidelines (VVSG).[2] These guidelines address some of the security and accessibility needs of elections. The EAC also accredits three test laboratories which manufacturers hire to review their equipment.[3] Based on reports from these laboratories the EAC certifies when voting equipment complies with the voluntary guidelines.
Twelve states require EAC certification for machines used in their states. Seventeen states require testing by an EAC-accredited lab, but not certification. Nine states and DC require testing to federal standards, by any lab. Four other states refer to federal standards but make their own decisions. The remaining eight states do not refer to federal standards.[4]
Certification takes two years, costs a million dollars, and is needed again for any equipment update, so election machines are a difficult market.[5]
A revision to the guidelines, known as the VVSG 1.1, was prepared in 2009 and approved in 2015.[2] Voting machine manufacturers can choose which guidelines they follow.[6] A new version has been written known as the VVSG 2.0 or the VVSG Next Iteration, which is being reviewed.[2]
Optical scan counting
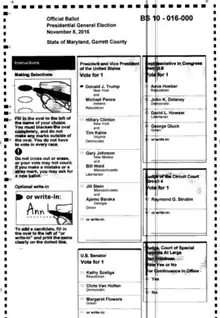
In an optical scan voting system, each voter's choices are marked on one or more pieces of paper, which then go through a scanner. The scanner creates an electronic image of each ballot, interprets it, creates a tally for each candidate, and usually stores the image for later review.
The voter may mark the paper directly, usually in a specific location for each candidate, then mail it or put it in a ballot box.
Or the voter may select choices on an electronic screen, which then prints the chosen names, usually with a bar code or QR code summarizing all choices, on a sheet of paper to put in the scanner.[7] This screen and printer is called an electronic ballot marker (EBM) or ballot marking device (BMD), and voters with disabilities can communicate with it by headphones, large buttons, sip and puff, or paddles, if they cannot interact with the screen or paper directly. Typically the ballot marking device does not store or tally votes. The paper it prints is the official ballot, put into a scanning system which counts the barcodes, or the printed names can be hand-counted, as a check on the machines.[8]
Most voters do not look at the machine-printed paper to ensure it reflects their choices. When there is a mistake, 93% of voters do not report it to poll workers.[9] No state requires central reporting of errors reported by voters, so the occasional report cannot lead to software correction. Hand-marked paper ballots more clearly have been reviewed by voters, but some places allow correction fluid and tape so ballots can be changed later.[10]
Two companies, Hart and Clear Ballot, have scanners which count the printed names, which voters had a chance to check, rather than bar codes and QR codes, which voters are unable to check.[11] When scanners use the bar code or QR code, the candidates are represented in the bar code or QR code as numbers, and the scanner counts those codes, not the names. If a bug or hack makes the numbering system in the ballot marking device different from the numbering system in the scanner, votes will be tallied for the wrong candidates.[11] This numbering mismatch has appeared with direct recording electronic machines (below).[12]
Errors in optical scans
Scanners have a row of photo-sensors which the paper passes by, and they record light and dark pixels from the ballot. A black streak results when a scratch or paper dust causes a sensor to record black continuously.[13][14] A white streak can result when a sensor fails.[15] In the right place, such lines can indicate a vote for every candidate or no votes for anyone. Some offices blow compressed air over the scanners after every 200 ballots to remove dust.[16]
Software can miscount; if it miscounts drastically enough, people notice and check. Staff rarely can say who caused an error, so they do not know whether it was accidental or a hack.
- In a 2020 election in Baltimore, Maryland, the private company which printed ballots shifted the location of some candidates on some ballots up one line, so the scanner looked in the wrong places on the paper and reported the wrong numbers. It was caught because a popular incumbent got implausibly few votes.[17]
- In a 2019 election in Northampton county, Pennsylvania, the software under-counted one candidate by 99%, reporting 164 votes, compared to 26,142 found in a subsequent hand-count, which changed the candidate's loss to a win.[18]
- In a 2018 New York City election when the air was humid, ballots jammed in the scanner, or multiple ballots went through a scanner at once, hiding all but one.[19]
- In a 2016 Maryland election, a comparison of two scanning systems on the same ballots revealed that (a) 1,972 ballot images were incorrectly left out of one system, (b) one system incorrectly ignored many votes for write-in candidates,[20] (c) shadows from paper folds were sometimes interpreted as names written in on the ballot, (d) the scanner sometimes pulled two ballots at once, scanning only the top one, (e) the ballot printers sometimes left off certain candidates, (f) voters often put a check or X instead of filling in an oval, which software has to adapt to, and (g) a scratch or dirt on a scanner sensor put a black line on many ballot images, causing the appearance of voting for more than the allowed number of candidates, so those votes were incorrectly ignored.[13][14]
- In 2016 Wisconsin elections statewide, some voting machines did not detect some of the inks used by voters.[21][22]
- In a 2016 Rhode Island election, machines were misprogrammed with only one ballot style, though there were two. Results were surprising enough so officials investigated and found the error.[23][22]
- In a 2014 Stoughton, Wisconsin, election, all voters' choices on a referendum were ignored, because the scanner was programmed to look in the wrong spot on the ballot.[16]
- In a 2010 New York election, 20,000 votes for governor and 30,000-40,000 votes for other offices were ignored, because the scanners overheated and disqualified the ballots by reading multiple votes in races where voters had properly only voted once.[24][25][26]
- Errors from 2002-2008 were listed and analyzed by the Brennan Center in 2010.[27]
- Security reviews and audits are discussed below.
Recreated ballots
Recreated ballots are paper[28] or electronic[29] ballots created by election staff when originals cannot be counted for some reason. Reasons include tears, water damage, folds which prevent feeding through scanners and voters selecting candidates by circling them or other abnormal marks.[30] Reasons also include citizens abroad who use the Federal Write-In Absentee Ballot because of not receiving their regular ballot in time. As many as 8% of ballots in an election may be recreated.[29]
When auditing an election, audits are done with the original ballots, not the recreated ones, to catch mistakes in recreating them.
Cost of scanning systems
If most voters mark their own paper ballots and one marking device is available at each polling place for voters with disabilities, Georgia's total cost of machines and maintenance for 10 years, starting 2020, has been estimated at $12 per voter ($84 million total). Pre-printed ballots for voters to mark would cost $4 to $20 per voter ($113 million to $224 million total machines, maintenance and printing). The low estimate includes $0.40 to print each ballot, and more than enough ballots for historic turnout levels. The high estimate includes $0.55 to print each ballot, and enough ballots for every registered voter, including three ballots (of different parties) for each registered voter in primary elections with historically low turnout.[31][32] The estimate is $29 per voter ($203 million total) if all voters use ballot marking devices, including $0.10 per ballot for paper.
The capital cost of machines in 2019 in Pennsylvania is $11 per voter if most voters mark their own paper ballots and a marking device is available at each polling place for voters with disabilities, compared to $23 per voter if all voters use ballot marking devices.[33] This cost does not include printing ballots.
New York has an undated comparison of capital costs and a system where all voters use ballot marking devices costing over twice as much as a system where most do not. The authors say extra machine maintenance would exacerbate that difference, and printing cost would be comparable in both approaches.[34] Their assumption of equal printing costs differs from the Georgia estimates of $0.40 or $0.50 to print a ballot in advance, and $0.10 to print it in a ballot marking device.[31]
Direct-recording electronic counting
A touch screen displays choices to the voter, who selects choices, and can change her mind as often as needed, before casting the vote. Staff initialize each voter once on the machine, to avoid repeat voting. Voting data and ballot images are recorded in memory components, and can be copied out at the end of the election.
The system may also provide a means for communicating with a central location for reporting results and receiving updates,[35] which is an access point for hacks and bugs to arrive.
Some of these machines also print names of chosen candidates on paper for the voter to verify. These names on paper can be used for election audits and recounts if needed. The tally of the voting data is stored in a removable memory component and in bar codes on the paper tape. The paper tape is called a Voter-verified paper audit trail (VVPAT). The VVPATs can be counted at 20–43 seconds of staff time per vote (not per ballot).[36][37]
For machines without VVPAT, there is no record of individual votes to check.
Errors in direct-recording electronic voting
This approach can have software errors. It does not include scanners, so there are no scanner errors. When there is no paper record, it is hard to notice or research most errors.
- The only forensic examination which has been done of direct-recording software files was in Georgia in 2020, and found that one or more unauthorized intruders had entered the files and erased records of what it did to them. In 2014–2017 an intruder had control of the state computer in Georgia which programmed vote-counting machines for all counties. The same computer also held voter registration records. The intrusion exposed all election files in Georgia since then to compromise and malware. Public disclosure came in 2020 from a court case.[38][39][40] Georgia did not have paper ballots to measure the amount of error in electronic tallies. The FBI studied that computer in 2017, and did not report the intrusion.[41][38]
- A 2018 study of direct-recording voting machines (iVotronic) without VVPAT in South Carolina found that every election from 2010–2018 had some memory cards fail. The investigator also found that lists of candidates were different in the central and precinct machines, so 420 votes which were properly cast in the precinct were erroneously added to a different contest in the central official tally, and unknown numbers were added to other contests in the central official tallies. The investigator found the same had happened in 2010. There were also votes lost by garbled transmissions, which the state election commission saw but did not report as an issue. 49 machines reported that their three internal memory counts disagreed, an average of 240 errors per machine, but the machines stayed in use, and the state evaluation did not report the issue, and there were other error codes and time stamp errors.[12][42]
- In a 2017 York County, Pennsylvania, election, a programming error in a county's machines without VVPAT let voters vote more than once for the same candidate. Some candidates had filed as both Democrat and Republican, so they were listed twice in races where voters could select up to three candidates, so voters could select both instances of the same name.[43] They recounted the DRE machines' electronic records of votes and found 2,904 pairs of double votes.[44]
- In a 2015 Memphis, Tennessee, city election, the central processing system lost 1,001 votes which showed on poll tapes posted at precincts: "at Unity Christian... precinct’s poll tape... 546 people had cast ballots... Shelby County’s first breakdown of each precinct’s voting... for Unity Christian showed only 330 votes. Forty percent of the votes had disappeared... At first it looked like votes were missing from not just one precinct but 20. After more investigation, he appeared to narrow that number to four... In all, 1,001 votes had been dropped from the election night count."[45]
- In a 2011 Fairfield Township, New Jersey, election a programming error in a machine without a VVPAT gave two candidates low counts. They collected more affidavits by voters who voted for them than the computer tally gave them, so a judge ordered a new election which they won.[46]
- Errors from 2002–2008 were listed and analyzed by the Brennan Center in 2010.[27]
- Security reviews and audits are discussed below.
Online, email and fax voting
Email, fax, phone apps, and web portals transmit information through the internet, between computers at both ends, so they are subject to errors and hacks at the origin, destination and in between. States that allow remote electronic voting in the United States are:[47]
- Hawaii allows email voting by any permanent absentee voter who has not received a ballot by five days before an election
- Idaho allows email and fax voting in declared emergencies
- Louisiana allows fax voting for voters with a disability
- Utah allows email and fax voting for those with disabilities
- Other states have tried or considered software, with problems discussed below.
The Uniformed and Overseas Citizens Absentee Voting Act (UOCAVA) lets overseas citizens and all military and merchant marine voters get ballots electronically (email, fax, or web site). They then submit ballots by mail to 20 states. Four states allow submission through secure web sites: AZ, CO (if needed), MO, and WV. These four and the remaining 27 states have a mix of rules allowing email or fax:[47] AK, CA, DE, DC, FL, HI, IN, IA, KS, LA, ME, MA, MS, MT, NE, NV, NJ, NM, NC, MD, OK, OR, RI, SC, TX (for danger, combat zones or space[48][49]), UT, and WA.[47]
Problems in online voting
Security experts have found security problems in every attempt at online voting,[50] [51] [52] [53] including systems in Australia,[54] Estonia,[55][56] Switzerland,[57] Russia,[58][59][60] and the United States.[61][50]
in 2019-2020 researchers found insecurities in online voting systems from Voatz,[61] [62] [63] and Democracy Live.[50][64]
In 2010, graduate students from the University of Michigan hacked into the District of Columbia online voting systems during an online voting mock test run and changed all the cast ballots to cater to their preferred candidates. This voting system was being tested for military voters and overseas citizens, allowing them to vote on the Web, and was scheduled to run later that year. It only took the hackers, a team of computer scientists, thirty-six hours to find the list of the government's passwords and break into the system.[65]
In March 2000 the 2000 Arizona Democratic presidential primary internet election was conducted over the internet using the private company votation.com.[66] Each registered member of the party received a personal identification number in the mail. They could vote in person or over the internet, using their PIN and answering two questions such as date and place of birth. During the election older browsers failed, but no hacks were identified.[67]
Electronic processing of postal and absentee ballots
Checking signatures on envelopes of absentee ballots is hard, and is often computerized in jurisdictions with many absentee ballots. The envelope is scanned, and the voter's signature on the outside of the envelope is instantly compared with one or more signatures on file. The machine sets aside non-matches in a separate bin. Temporary staff then double-check the rejections, and in some places check the accepted envelopes too.[68]
Error rates of computerized signature reviews are not published. "A wide range of algorithms and standards, each particular to that machine's manufacturer, are used to verify signatures. In addition, counties have discretion in managing the settings and implementing manufacturers' guidelines… there are no statewide standards for automatic signature verification… most counties do not have a publicly available, written explanation of the signature verification criteria and processes they use"[68]
Handwriting experts agree "it is extremely difficult for anyone to be able to figure out if a signature or other very limited writing sample has been forged,"[69] The National Vote at Home Institute reports that 17 states do not mandate a signature verification process.[70] The Election Assistance Commission says that machines should be set only to accept nearly perfect signature matches, and humans should doublecheck a sample, but EAC does not discuss acceptable error rates or sample sizes.[71]
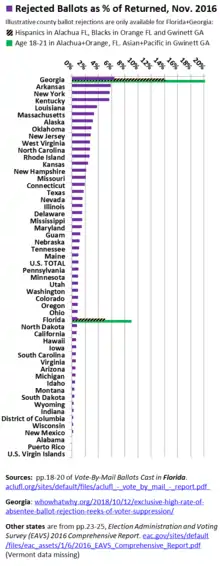
In the November 2016 general election, rejections ranged from none in Alabama and Puerto Rico, to 6% of ballots returned in Arkansas, Georgia, Kentucky and New York.[72] [73] Where reasons for rejection were known, in 2018, 114,000 ballots arrived late, 67,000 failed signature verification, 55,000 lacked voter signatures, and 11,000 lacked witness signatures in states which require them.[74] The intent of the signature verification step was to catch and reject forged signatures on ballot envelopes.[75][76]
The highest error rates in signature verification are found among lay people, higher than for computers, which in turn make more errors than experts.[77] Researchers have published error rates for computerized signature verification. They compare different systems on a common database of true and false signatures. The best system falsely rejects 10% of true signatures, while it accepts 10% of forgeries. Another system has error rates on both of 14%, and the third-best has error rates of 17%.[78][79] It is possible to be less stringent and reject fewer true signatures, at the cost of also rejecting fewer forgeries, which means erroneously accepting more forgeries.[80] Vendors of automated signature verification claim accuracy, and do not publish their error rates.[81][82][83][84]
Voters with short names are at a disadvantage, since even experts make more mistakes on signatures with fewer "turning points and intersections."[85]
State and local websites for election results
Election offices display election results on the web by transferring USB drives between offline election computers, and online computers which display results to the public.[86] USB drives can take infections from the online computers to the election computers.[87][88] Local governments communicate electronically with their state governments so the state can display results, with the result that problems at the state level can affect all or many local offices.
Election-reporting websites run software to aggregate and display results. These have had programming errors which showed erroneous partial results during the evening,[89] and the wrong winner.[90]
Before the 2016 general election, Russians gained access to at least one employee's account[91] at a vendor which manages election-reporting websites.[92] During the 2018 general election, a hacker in India gained administrative access to the Alaska election-reporting website.[93][94]
Studies by McAfee and ProPublica in 2020 found that most election websites have inadequate security. McAfee analyzed swing states.[95] ProPublica analyzed Super Tuesday states.[96] They found many offices using outdated, insecure, dangerous and inappropriate software, including unsupported operating systems, and using the same few web hosts, which they said is dangerous for critical infrastructure, since finding a flaw in one can lead to access to them all.[96] They criticized offices for not using https encryption, and for public sitenames ending in .com or .org, since it leads voters to trust sites which are not .gov, and voters can easily be tricked by a similar name.[97]
Election security

Decentralized system
In 2016 Homeland Security and the Director of National Intelligence said that United States elections are hard to hack, because they are decentralized, with many types of machines and thousands of separate election offices operating under 51 sets of state laws.[98][99] Others have made similar statements.[100]
An official at the Center for Strategic and International Studies said a nation state would target hacks in key counties.[101] A McAfee expert said decentralization makes defense hard and for "a very determined group, trying to compromise this system, I think it ends up playing more into their favor than against them."[101] Each city or county election is run by one office, and a few large offices affect state elections. County staff cannot in practice defend against foreign governments.[102]
Security reviews
The Brennan Center summarized almost 200 errors in election machines from 2002-2008, many of which happened repeatedly in different jurisdictions, which had no clearinghouse to learn from each other.[27] More errors have happened since then.
Machines in use are not examined to determine if they have been hacked, so no hacks of machines in use have been documented. Researchers have hacked all machines they have tried, and have shown how they can be undetectably hacked by manufacturers, election office staff, pollworkers, voters and outsiders and by the public.[103] The public can access unattended machines in polling places the night before elections.[104] Some of the hacks can spread among machines on the removable memory cards which tell the machines which races to display, and carry results back to the central tally location.
The CEO of Free and Fair, an open source vendor, said the cheapest way to improve security is for each election office to hire a computer student as a white hat hacker to conduct penetration tests.[105]
Ohio
In December 2007 the Ohio Secretary of State Jennifer Brunner released the results of a comprehensive review of Ohio's electronic voting technology. The study examined electronic voting systems – both touch-screen and optical scan – from Election Systems & Software, Hart InterCivic, and Premier Election Systems.[106] Three teams of security researchers, based at the Pennsylvania State University, the University of Pennsylvania, and WebWise Security, Inc., conducted the security reviews. The teams had access to voting machines and software source code from the three vendors and performed source code analysis and security penetration testing with the aim of identifying security problems that might affect the integrity of elections that use the equipment.
The 2007 Ohio report noted that all
"election systems rely heavily on third party software that implement interfaces to the operating systems, local databases, and devices such as optical scanners... the construction and features of this software is unknown, and may contain undisclosed vulnerabilities such trojan horses or other malware."[106]
Thus election machines are subject to "class breaks," which are attacks, deliverable by annual updates, against the underlying operating systems and drivers.[107] The 2016 federal certification of ES&S notes that it uses Windows 7, Windows Server 2008, Excel 2007, Adobe Acrobat version 9.0 (support ended 2013), WSUS Offline Update Utility 8.8 (issued 2013[108]) and other off the shelf software.[109]
Michigan
ES&S[110] and Dominion Voting Systems[111] provide results to election officials in Excel without hash values, so malware (or unsupervised staff) can change results before publication. Michigan requires election systems to provide results in spreadsheet format; it neither requires nor forbids hash values.[110]
California
In August 2007, California Secretary of State Debra Bowen announced results of a "top-to-bottom review" of security of all electronic voting systems in the state, including Diebold Election Systems, Hart InterCivic, Sequoia Voting Systems and Elections Systems and Software.[112] An August 2 report by computer security experts from the University of California found flaws in voting system source code. On July 27 "red teams" reported on "worst case" Election Day scenarios, where they identified vulnerabilities to tampering or error. The Top to Bottom review also included a comprehensive review of manufacturer documentation as well as a review of accessibility features and alternative language requirements.
The California security experts found significant security flaws in all of the manufacturers' voting systems, flaws that could allow a single non-expert to compromise an entire election.[113] The July and August reports found that three of the tested systems fell far short of the minimum requirements specified in the EAC 2005 Voluntary Voting System Guidelines (VVSG). On August 3, 2007, Bowen decertified machines that were tested, and also the ES&S InkaVote machine, which was not included in the review because the company submitted it past the deadline for testing. Some of the systems tested were conditionally recertified with new stringent security requirements imposed.[114] The companies in question had until the February 2008 California Presidential Primaries to fix their security issues and ensure that election results could be closely audited.
California has continued to report on security of newer election machines.[115]
New Jersey
In 2006, Princeton University computer scientists studied security of the Premier Election Solutions (formerly Diebold Election Systems) AccuVote-TSx voting system for a group of New Jersey counties. Their results showed that the AccuVote-TSx was insecure and could be "installed with vote-stealing software in under a minute." The scientists also said that machines can transmit computer viruses from one to another "during normal pre- and post-election activity."[116]
Texas
Texas annually reviews software.[117] In 2020 the review noted that procedures did not ensure the ES&S software in use was the same as the software approved by the Election Assistance Commission.[118]
Audits
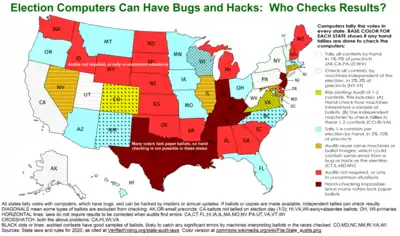
Five states check all contests by hand tallies in a small percent of locations, AK, CA, PA, UT, WV, though California excludes about half the ballots, the ones counted after election day, and Alaska excludes small precincts. Two states check all contests by machines independent of the election machines, in a small percent of locations, NY, VT. Seventeen states check one or a few contests by hand, usually federal races and the governor; most local contests are not checked. Four states reuse the same machines or ballot images as the election, so errors can persist, CT, IL, MD, NV. Sixteen states do not require audits, or only in special circumstances. In seven states many voters still lack paper ballots, so audits are not possible. IN, KY, LA, MS, NJ, TN, TX.[119]
Even where audits are done, no state has adequate security on the paper ballots, so they can be damaged to impede audits, or altered to match erroneous machine tallies.[120] Even insiders have breached security.[121][122]
Public attitudes
The Pew Research Center found in October 2018 wide mistrust of election security in both parties, especially among Democrats
- 8% of voters were "very confident that election systems are secure from hacking and other technological threats."
- 37% were "somewhat confident", and the remaining 55% were not confident
- 13% of Republicans were very confident, and 41% were not confident
- 4% of Democrats were very confident, and 66%% were not confident[123]
An MIT professor's survey found that Republicans think domestic hackers are more likely than foreigners; Democrats think the opposite.[124]
Stanford and Wisconsin researchers in 2019 found that only 89% of voters disapprove if a foreign country would "hack into voting machines and change the official vote count to give [a] candidate extra votes" and the candidate wins. This 89% disapproval is not much more than the 88% who disapprove of a foreign country making campaign contributions and 78-84% against them spreading lies. Only 73-79% disapprove if their party got help, while 94-95% disapprove of the other party getting help. If a foreign country thought about interfering, but did not, 21% distrust the results anyway. This rises only to 84% distrusting final results after a foreign country hacked and changed results.[125]
For any of the foreign actions (hacks, contributions or lies), 72% of voters support economic sanctions, 59% support cutting diplomatic relations, 25% support a military threat, and 15% support a military strike. There was less support for action, by 4-20 percentage points, if the foreign country helped one's own party win, so the researchers point out that retaliation is unlikely, since there is little support for it in a winning party. Deep investigation creates more certainty about who is to blame, which they find raises support for retaliation very little. They randomly listed China, Pakistan or Turkey as the interfering country, and do not report any different reactions to them.[125]
A Monmouth University poll in May 2019 found that 73% thought Russia interfered in the 2016 election (not necessarily by hacking), 49% thought it damaged American democracy a lot, 57% thought Russia interfered in the 2018 election, and 60% thought the US government is not doing enough to stop it. Margin of error is ±3.5%.[126]
Election companies
Three vendors sell most of the machines used for voting and for counting votes. As of September 2016, the American Election Systems & Software (ES&S) served 80 million registered voters, Canadian Dominion Voting Systems 70 million, American Hart InterCivic 20 million, and smaller companies less than 4 million each.[5]
More companies sell signature verification machines: ES&S, Olympus, Vantage, Pitney Bowes, Runbeck, and Bell & Howell.[68]
Amazon provides election websites in 40 states, including election-reporting sites in some of them.[127] A Spanish company, Scytl, manages election-reporting websites statewide in 12 U.S. states, and in another 980 local jurisdictions in 28 states.[128] Another website management company is VR Systems, active in 8 states.[129] Maryland's election website is managed by a company owned by an associate of Russian President Putin.[130]
Timeline of development
- 1964: The Norden-Coleman optical scan voting system, the first such system to see actual use, was adopted for use in Orange County, California.[131]
- 1974: The Video Voter, the first DRE voting machine used in a government election, developed by the Frank Thornber Company in Chicago, Illinois, saw its first trial use in 1974 near Chicago.[132]
- Mar. 1975:The U.S. Government is given a report by Roy Saltman, a consultant in developing election technology and policies, in which the certification of voting machines is analyzed for the first time.
- August 28, 1986: The Uniformed and Overseas Citizen Absentee Voting Act of 1986 (UOCAVA) requires that US states allow certain groups of citizens to register and vote absentee in elections for federal offices.[133]
- 1990: The FEC (Federal Election Commission) released a universalized standard for computerized voting.
- 1996: The Reform Party uses I-Voting (Internet Voting) to select their presidential candidate. This election is the first governmental election to use this method in the U.S.[134]
- May 2002:The FEC revised the standards established for electronic voting from 1990.
- Nov 2004: 4,438 of votes in the general election is lost by North Carolina’s electronic voting machines. The machines continued to count electronic votes past the device's memory capacity and the votes were irretrievably lost.
- Dec 2005: Black Box Voting showed how easy it is to hack an electronic voting system. Computer experts in Leon County, Fl lead a simulation where they changed the outcome of a mock election by tampering with the tabulator without leaving evidence of their actions.
- September 13, 2006: It was demonstrated that Diebold Electronic Voting Machine can be hacked in less than a minute. Princeton's Professor of Computer Science, Edward Felten who installed a malware which could steal votes and replace them with fraudulent numbers without physically coming in contact with the voting machine or its memory card. The malware can also program a virus that can spread from machine to machine.
- September 21, 2006: The governor of Maryland, Bob Ehrlich (R), advised against casting electronic votes as an alternative method for casting paper absentee ballots. This was a complete turn around since Maryland became one of the first states to accept electronic voting systems statewide during his term.
- September 3, 2009: Diebold, responsible for much of the technology in the election-systems business, sells their hold to Election Systems & Software, Inc for $5 Million, less than 1/5 of its price seven years earlier.[135]
- October 28, 2009: The federal Military and Overseas Voters Empowerment Act (MOVE) requires US states to provide ballots to UOCAVA voters in at least one electronic format (email, fax, or an online delivery system).[136]
- January 3, 2013: Voter Empowerment Act of 2013 – This act requires each US state to make available public websites for online voter registration.[137]
- Spring 2019: Department of Defense DARPA announces $10 million contract for secure, open-source election system prototypes based on the agency's SSITH secure hardware platform work: a touch screen ballot-marking device to demo at the annual DEF CON hacker conference in summer 2019 and an optical scan system to read hand-marked paper ballots targeted for DEF CON 2020.[138][139][140]
Legislation
In the summer of 2004, the Legislative Affairs Committee of the Association of Information Technology Professionals issued a nine-point proposal for national standards for electronic voting.[141] In an accompanying article, the committee's chair, Charles Oriez, described some of the problems that had arisen around the country.[142][143]
Legislation has been introduced in the United States Congress regarding electronic voting, including the Nelson-Whitehouse bill. This bill would appropriate as much as 1 billion dollars to fund states' replacement of touch screen systems with optical scan voting system. The legislation also addresses requiring audits of 3% of precincts in all federal elections. It also mandates some form of paper trail audits for all electronic voting machines by the year 2012 on any type of voting technology.[144]
Another bill, HR.811 (The Voter Confidence and Increased Accessibility Act of 2003), proposed by Representative Rush D. Holt, Jr., a Democrat from New Jersey, would act as an amendment to the Help America Vote Act of 2002 and require electronic voting machines to produce a paper audit trail for every vote. The U.S. Senate companion bill version introduced by Senator Bill Nelson from Florida on November 1, 2007, necessitates the Director of the National Institute of Standards and Technology to continue researching and to provide methods of paper ballot voting for those with disabilities, those who do not primarily speak English, and those who do not have a high literacy rating. Also, it requires states to provide the federal office with audit reports from the hand counting of the voter verified paper ballots. Currently, this bill has been turned over to the United States Senate Committee on Rules and Administration and a vote date has not been set.[145]
During 2008, Congressman Holt, because of an increasing concern regarding the insecurities surrounding the use of electronic voting technology, submitted additional bills to Congress regarding the future of electronic voting. One, called the "Emergency Assistance for Secure Elections Act of 2008" (HR5036), states that the General Services Administration will reimburse states for the extra costs of providing paper ballots to citizens, and the costs needed to hire people to count them.[146] This bill was introduced to the House on January 17, 2008.[147] This bill estimates that $500 million will be given to cover costs of the reconversion to paper ballots; $100 million given to pay the voting auditors; and $30 million given to pay the hand counters. This bill provides the public with the choice to vote manually if they do not trust the electronic voting machines.[146] A voting date has not yet been determined.
The Secure America's Future Elections Act or the SAFE Act (HR 1562) was among the relevant legislation introduced in the 115th Congress. The bill's provisions include designation of the infrastructure used to administer elections as critical infrastructure; funding for states to upgrade the security of the information technology and cybersecurity elements of election-related IT systems; and requirements for durable, readable paper ballots and manual audits of results of elections.
References
- Hedlin, Simon (November 3, 2015). "Do Long Ballots Offer Too Much Democracy?". Atlantic. Retrieved July 8, 2020.
- "Voluntary Voting System Guidelines". U.S. Election Assistance Commission. Retrieved July 9, 2020.
- "Accredited Laboratories". U.S. Election Assistance Commission. Retrieved July 8, 2020.
- "Voting System Standards, Testing and Certification". www.ncsl.org. Retrieved July 8, 2020.
- Hitt, Lorin, Simran Ahluwalia, Matthew Caulfield, Leah Davidson, Mary Margaret Diehl, Alina Ispas, and Michael Windle. "The Business of Voting Market Structure and Innovation in the Election Technology Industry". Penn Wharton Public Policy Initiative. Retrieved July 7, 2020.
- "Free Speech For People and National Election Defense Coalition to U.S. Election Assistance Commission: Don't Let Voting Machine Vendors Use Obsolete Standards". Free Speech For People. June 7, 2019. Retrieved July 9, 2020.
- "Ballot Marking Devices". Verified Voting. Retrieved February 28, 2020.
- Cohn, Jennifer (May 5, 2018). "What is the latest threat to democracy?". Medium. Retrieved February 28, 2020.
- Bernhard, Matthew, Allison McDonald, Henry Meng, Jensen Hwa, Nakul Bajaj, Kevin Chang, J. Alex Halderman (December 28, 2019). "Can Voters Detect Malicious Manipulation of Ballot Marking Devices?" (PDF). Halderman. Retrieved February 28, 2020.
- "2 CCR 20983(c)(6)" (PDF). California Sec. of State. October 1, 2020. Retrieved October 5, 2020.
- Perez, Edward, Joy London, Gregory Miller (March 2019). "Georgia State Election Technology Acquisition, Assessing Recent Legislation in Light of Planned Procurement" (PDF). OSET Institute. Retrieved March 5, 2020.
- Buell, Duncan (December 23, 2018). Analysis of the Election Data from the 6 November 2018 General Election in South Carolina (PDF). League of Women Voters of South Carolina (Report). Retrieved February 5, 2020.
- Walker, Natasha (February 13, 2017). "2016 Post-Election Audits in Maryland" (PDF). Elections Advisory Commission. Retrieved February 27, 2020.
- Ryan, Tom and Benny White (November 30, 2016). "Transcript of Email on Ballot Images" (PDF). Pima County, AZ. Retrieved February 15, 2020.
- Gideon, John (July 5, 2005). "Hart InterCivic Optical-Scan Has A Weak Spot". www.votersunite.org. Retrieved February 15, 2020.
- McKim, Karen; 2015 (February 17, 2015). "Unregistered Dust Bunnies May be Voting in Wisconsin Elections: Stoughton Miscount Update". Wisconsin Grassroots Network. Retrieved June 26, 2020.CS1 maint: numeric names: authors list (link)
- Davis, Emily Opilo, Talia Richman, Phil (June 3, 2020). "Concern from candidates, officials as error creates delay in release of returns; Dixon leads in Baltimore mayoral count". Baltimore Sun. Retrieved July 30, 2020.
- Corasaniti, Nick (November 30, 2019). "A Pennsylvania County's Election Day Nightmare Underscores Voting Machine Concerns". The New York Times. ISSN 0362-4331. Retrieved February 15, 2020.
- MacDougall, Ian (November 7, 2018). "What Went Wrong at New York City Polling Places? It Was Something in the Air. Literally". ProPublica. Retrieved February 18, 2020.
- Lamone, Linda (December 22, 2016). "Joint Chairman's Report on the 2016 Post-Election Tabulation Audit" (PDF). Maryland State Board of Elections. Retrieved February 15, 2020.
- Sommerhauser, Mark (September 27, 2017). "State to end use of ballot-counting machine that had flaw highlighted in recount". Wisconsin State Journal. Retrieved January 9, 2021.
- Garland, Lynn (2018). "Principles and Best Practices for Post-Election Tabulation Audits" (PDF). Election Audits. Retrieved January 9, 2021.
- Gregg, Katherine (September 14, 2017). "Vote-tally audits, criminal-sentencing overhaul on RI lawmakers' agenda". Providence Journal. Retrieved January 9, 2021.
- Hamilton, Colby (May 9, 2012). "Machine Casts Phantom Votes in the Bronx, Invalidating Real Ones: Report". WNYC New York Public Radio. Retrieved June 26, 2020.
- Keefe, Hohn (December 6, 2011). "Thousands of NY Votes Tossed Over Ballot Confusion". WNYC New York Public Radio. Archived from the original on March 31, 2015. Retrieved June 26, 2020.
- Norden, Larry, and Sundeep Iyer (December 5, 2011). "Design Deficiencies and Lost Votes". Brennan Center for Justice. Retrieved June 26, 2020.
- Norden, Lawrence (September 16, 2010). "Voting system failures: a database solution" (PDF). Brennan Center, NYU. Retrieved July 7, 2020.
- "observers from both political parties there... ballots have to be recreated in every election for a number of reasons, ranging from damaged mail-in ballots, to early voters who use pencils which can’t be read by ballot tabulators." Jordan, Ben (November 7, 2018). "MKE Election Commission responds to criticism". WTMJ TV Milwaukee. Retrieved May 17, 2020.
- "With the new digital procedure, staff will be able to fix whatever race couldn’t be counted, instead of duplicating a voter’s entire ballot." White, Rebecca (November 18, 2019). "One Washington County Plans to Speed Vote Counting with Tech". Government Technology. Retrieved May 17, 2020.
- Miller, Steve (November 7, 2006). "Oddly marked ovals bane of poll workers' day". Rapid City Journal. Retrieved May 17, 2020.
- Perez, Edward, and Gregory Miller (March 2019). "Georgia State Election Technology Acquisition, A Reality Check". OSET Institute. Retrieved March 6, 2020.
- Fowler, Stephen. "Here's What Vendors Say It Would Cost To Replace Georgia's Voting System". Georgia Public Broadcasting. Retrieved February 28, 2020.
- Deluzio, Christopher, Kevin Skoglund (February 28, 2020). "Pennsylvania Counties' New Voting Systems Selections: An Analysis" (PDF). University of Pittsburgh. Retrieved February 28, 2020.
- "Paper Ballots Costs". www.nyvv.org. Retrieved February 28, 2020.
- 2005 Voluntary Voting System Guidelines Archived February 8, 2006, at the Wayback Machine from the US Election Assistance Commission
- Theisen, Ellen (June 14, 2005). "Cost Estimate for Hand Counting 2% of the Precincts in the U.S." (PDF). VotersUnite.org. Retrieved February 14, 2020.
- "Voter Verified Paper Audit Trail Pilot Project Report" (PDF). Georgia Secretary of State. April 10, 2007. Retrieved February 15, 2020.
- Lamb, Logan (January 14, 2020). "Supplemental Declaration of Logan Lamb" (PDF). CourtListener. Retrieved February 3, 2020.
- "Coalition Plaintiffs' Status Report". Coalition for Good Governance. January 16, 2020. pp. 237–244. Retrieved February 3, 2020.
- Bajak, Frank (January 16, 2020). "Expert: Georgia election server showed signs of tampering". Associated Press. Retrieved February 3, 2020.
- Zetter, Kim. "Will the Georgia Special Election Get Hacked?". Politico. Retrieved February 16, 2020.
- Freed, Benjamin (January 7, 2019). "South Carolina voting machines miscounted hundreds of ballots, report finds". Scoop News Group. Retrieved February 5, 2020.
- Kessler, Brandie, Teresa Boeckel and Dylan Segelbaum; Boeckel, Teresa; Segelbaum, Dylan (November 7, 2017). "'Redo' of some York County races – including judge – possible after voting problems". York Daily Record. Retrieved March 11, 2020.
- Lee, Rick (November 20, 2017). "York Co. election judicial winners: Kathleen Prendergast, Clyde Vedder, Amber Anstine Kraft". York Daily Record. Retrieved March 11, 2020.
- Riley, Michael, Jordan Robertson, and David Kocieniewski (September 29, 2016). "The Computer Voting Revolution Is Already Crappy, Buggy, and Obsolete". Bloomberg.com. Retrieved October 30, 2020.
- Thibodeau, Patrick (October 5, 2016). "If the election is hacked, we may never know". ComputerWorld. Retrieved February 18, 2020.
- "Electronic Transmission of Ballots". www.ncsl.org. Retrieved July 8, 2020.
- "Astronauts beam votes home". CNN. November 2, 2010. Archived from the original on March 3, 2016.
- James, Kate (November 2, 2010). "Astronauts Cast Vote From Space Thanks to 1997 Texas Law". Gather.com. Archived from the original on May 11, 2011. Retrieved November 2, 2010.
- Appel, Andrew (June 8, 2020). "Democracy Live internet voting: unsurprisingly insecure, and surprisingly insecure". Princeton University. Retrieved June 23, 2020.
- "Internet Voting". Verified Voting. Retrieved June 20, 2020.
- "Secure Internet voting will likely not be feasible in the near future... At the present time, the Internet (or any network connected to the Internet) should not be used for the return of marked ballots" National Academies of Sciences (September 6, 2018). "Securing the Vote: Protecting American Democracy". Retrieved June 23, 2020.
- "Electronic ballot return faces significant security risks to the confidentiality, integrity, and availability of voted ballots. These risks can ultimately affect the tabulation and results and, can occur at scale... Even with ... technical security considerations, electronic ballot return remains a high-risk activity." Election Assistance Commission, National Institute of Standards and Technology, FBI, Cybersecurity & Infrastructure Security Agency (May 11, 2020). "Risk Management for Electronic Ballot Delivery, Marking, and Return" (PDF). Retrieved June 23, 2020.CS1 maint: multiple names: authors list (link)
- Halderman, J. Alex, and Vanessa Teague (August 13, 2015). The New South Wales iVote System: Security Failures and Verification Flaws in a Live Online Election. International Conference on E-Voting and Identity. arXiv:1504.05646. doi:10.1007/978-3-319-22270-7_3.
- Springall, Drew; Finkenauer, Travis; Durumeric, Zakir; Kitcat, Jason; Hursti, Harri; MacAlpine, Margaret; Halderman, Alex, Security Analysis of the Estonian Internet Voting System, retrieved December 3, 2017
- "The OSCE/ODIHR EAM was made aware of a program that could, if it was running on a voter’s computer, change the vote without the possibility for the voter to detect it. The case was brought to the attention of the project manager who assessed this threat to be theoretically plausible but nearly impossible to implement in reality." "Estonia Parliamentary Elections OSCE/ODIHR Election Assessment Mission Report" (PDF). OSCE. March 6, 2011. Retrieved June 20, 2020.
- Zetter, Kim (March 12, 2019). "Researchers Find Critical Backdoor in Swiss Online Voting System". Vice. Retrieved June 20, 2020.
- Gupta, Manhar. "Russia's Blockchain Voting Turned Into A Fiasco". Cryptotrends.
- Gaudry, Pierrick, and Alexander Golovnev (February 10, 2020). Breaking the Encryption Scheme of the Moscow Internet Voting System (PDF). Financial Cryptography 2020 – via International Financial Cryptography Association.
- Anderson, Ross (February 21, 2020). "Electronic voting systems". The RISKS Digest. 31 (59) – via Newcastle University.
- Zetter, Kim (February 13, 2020). "'Sloppy' Mobile Voting App Used in Four States Has 'Elementary' Security Flaws". VICE. Retrieved June 23, 2020.
- Specter, Michael A., James Koppel, Daniel Weitzner (February 12, 2020). "The Ballot is Busted Before the Blockchain: A Security Analysis of Voatz, the First Internet Voting Application Used in U.S. Federal Elections" (PDF). Massachusetts Institute of Technology. Retrieved June 23, 2020.
- Halper, Evan (May 16, 2019). "The vote-by-phone tech trend is scaring the life out of security experts". San Diego Union Tribune. Retrieved June 23, 2020.
- Parks, Miles (February 28, 2020). "States Expand Internet Voting Experiments Amid Pandemic, Raising Security Fears". National Public Radio. Retrieved June 23, 2020.
- Wheaton, Sarah. "Voting Test Falls Victim to Hackers". The New York Times. Archived from the original on June 27, 2017. Retrieved February 20, 2015.
- "Arizona Democratic Party Selects Votation.com to Hold World's First Legally-Binding Public Election Over the Internet". www.thefreelibrary.com. Retrieved December 19, 2017.
- "How online voting works". usatoday.com. March 10, 2000.
- "Signature Verification and Mail Ballots: Guaranteeing Access While Preserving Integrity" (PDF). Stanford University. April 15, 2020. Retrieved June 1, 2020.
- Armitage, Susie (November 5, 2018). "Handwriting Disputes Cause Headaches for Some Absentee Voters". ProPublica. Retrieved June 1, 2020.
- "Vote at Home Policy Actions: 1 and 2 Stars" (PDF). National Vote at Home Institute. May 2020. Retrieved June 18, 2020.
- "Signature Verification and Cure Process" (PDF). US Election Assistance Commission. May 20, 2020. Retrieved June 17, 2020.
- "THE ELECTION ADMINISTRATION AND VOTING SURVEY (EAVS) 2016 Comprehensive Report" (PDF). Election Assistance Commission. June 28, 2017. Retrieved June 12, 2020.
- Salame, Richard (June 18, 2020). "As States Struggle With Vote-by-Mail, "Many Thousands, If Not Millions" of Ballots Could Go Uncounted in November". Type Investigations. Retrieved June 18, 2020.
- "Election Administration and Voting Survey (EAVS) 2018 Comprehensive report" (PDF). Election Assistance Commission. Retrieved June 12, 2020.
- Cervantes, Lauren (October 8, 2020). "How Seminole County election officials detect voter fraud". ClickOrlando. Retrieved December 2, 2020.
- Jennings, Nicole (October 29, 2020). "A ballot's journey at King County Elections headquarters". MyNorthwest. Retrieved December 2, 2020.
- Srihari, Sargur N. (August 12, 2010). "Computational Methods for Handwritten Questioned Document Examination 1 FINAL REPORT to Dept. of justice Award Number: 2004-IJ-CX-K050". CiteSeerX 10.1.1.186.175. Cite journal requires
|journal=(help) - These systems handle scanned ("offline") signatures from multiple people ("WI, writer-independent"). Hafemann, Luiz G., Robert Sabourin and Luiz S. Oliveira (October 16, 2017). Offline Handwritten Signature Verification - Literature Review. pp. 1–8. arXiv:1507.07909. doi:10.1109/IPTA.2017.8310112. ISBN 978-1-5386-1842-4. S2CID 206932295.
- Bibi, Kiran; Naz, Saeeda; Rehman, Arshia (January 1, 2020). "Biometric signature authentication using machine learning techniques: Current trends, challenges and opportunities". Multimedia Tools and Applications. 79 (1): 289–340. doi:10.1007/s11042-019-08022-0. ISSN 1573-7721. S2CID 199576552.
- Igarza, Juan; Goirizelaia, Iñaki; Espinosa, Koldo; Hernáez, Inmaculada; Méndez, Raúl; Sanchez, Jon (November 26, 2003). Online Handwritten Signature Verification Using Hidden Markov Models. CIARP 2003. 2905. pp. 391–399. doi:10.1007/978-3-540-24586-5_48.
- "SignatureXpert for Vote by Mail" (PDF). Parascript. May 5, 2020. Retrieved July 21, 2020.
- "Agilis Ballot Packet Sorting System" (PDF). Runbeck. November 7, 2019.
- "Criterion Elevate". www.fluenceautomation.com. Retrieved July 21, 2020.
- "Vote-By-Mail Best Practices Webinar Series". www2.bluecrestinc.com. Retrieved July 21, 2020.
- Sita, Jodi; Found, Bryan; Rogers, Douglas K. (September 2002). "Forensic Handwriting Examiners' Expertise for Signature Comparison". Journal of Forensic Sciences. 47 (5): 1117–24. doi:10.1520/JFS15521J. ISSN 0022-1198. PMID 12353558.
- Marks, Marilyn (June 14, 2017). "Georgia's Voting System, the Internet, and the Meaning of "Is"". Medium. Retrieved July 30, 2020.
- Microsoft Security Intelligence Report Volume 11, January-June, 2011.
- "The State of USB Drive Security: Study of IT and IT Practitioners". news.bloomberglaw.com. Retrieved July 30, 2020.
- Reding, Shawna (July 14, 2020). "Texas Secretary of State website fixes technical glitch in runoff election results". KVUE - ABC. Retrieved July 30, 2020.
- Cottrill, Clarissa (May 18, 2018). "Official results in: Hammer, Redding win judge seats". Journal-News.net. Retrieved July 30, 2020.
- Cole, Matthew; Esposito, Richard; Biddle, Sam; Grim, Ryan (June 5, 2017). "Top-Secret NSA Report Details Russian Hacking Effort Days Before 2016 Election". Retrieved July 30, 2020.
- Sherman, Amy (October 19, 2016). "Premature posting of election results was mistake, not a crime". Miami Herald. Retrieved July 30, 2020.
- Herz, Nathaniel (May 8, 2018). "Hackers broke partway into Alaska's election system in 2016. Officials say no damage was done". Anchorage Daily News. Retrieved July 30, 2020.
- Newman, Lily Hay (March 16, 2020). "'Kill Chain': HBO's Election Security Doc Stresses Urgency". Wired. ISSN 1059-1028. Retrieved July 30, 2020.
- "McAfee Research Reveals Election Website Security Shortcomings in 2020 Battleground States". www.mcafee.com. February 3, 2020. Retrieved July 31, 2020.
- Gillum, Jack (March 2, 2020). "Is your local election website safe? Investigation finds security risks in old systems". Raleigh News & Observer.
- "Majority of Election Websites in Battleground States Failing in Cybersecurity". Security Magazine. February 4, 2020. Retrieved July 31, 2020.
- "Joint Statement from the Department Of Homeland Security and Office of the Director of National Intelligence on Election Security". Department of Homeland Security. October 7, 2016. Retrieved July 8, 2020.
- Brandom, Russell (October 28, 2016). "How worried should we be about election hacking?". The Verge. Retrieved July 8, 2020.
- Riley, Michael, Jordan Robertson, and David Kocieniewski (September 29, 2016). "The Computer Voting Revolution Is Already Crappy, Buggy, and Obsolete". Bloomberg.com. Retrieved October 13, 2020.
- Good, Chris (October 31, 2018). "When it comes to election cybersecurity, decentralized system is viewed as both blessing and curse". ABC News. Retrieved July 8, 2020.
- McManus, Doyle (June 16, 2019). "Column: Norway, if you're listening: Feel free to hack our presidential race". Los Angeles Times. Retrieved July 9, 2020.
- Blaze, Matt, Harri Hursti , Margaret Macalpine, Mary Hanley, Jeff Moss, Rachel Wehr, Kendal L Spencer, Christopher Ferris (September 26, 2019). "DEF CON 27 Voting Machine Hacking Village" (PDF). Defcon. Retrieved March 11, 2020.
- Felten, Ed (June 8, 2010). "NJ Voting Machines Left Unattended, Despite Court Opinion". Princeton University. Retrieved July 8, 2020.
- Gross, Grant (October 5, 2016). "5 ways to improve voting security in the U.S." ComputerWorld. Retrieved September 3, 2020.
- McDaniel; et al. (December 7, 2007). EVEREST: Evaluation and Validation of Election-Related Equipment, Standards and Testing (PDF) (Report). Retrieved February 5, 2020.
- Schneier, Bruce (January 3, 2017). "Class Breaks - Schneier on Security". www.schneier.com. Retrieved September 3, 2020.
- "WSUS Offline Update 8.8 brings IE11 to Windows 7". en.secnews.gr. November 18, 2013. Retrieved September 8, 2020.
- "Certificate of Conformance ES&S Unity 3.4.1.4 Election Systems & Software" (PDF). US Election Assistance Commission. August 26, 2016. Retrieved September 8, 2020.
- "RFP No. 007116B0007029 Election Systems & Software, Exhibit A, Attachment 1.1 Voting System HARDWARE Technical Requirements, DS200, pages 83, 114" (PDF). Michigan Secretary of State. January 25, 2017.
- "Democracy Suite® EMS Results Tally & Reporting User Guide Version: 5.11-CO::7, pages 9, 55" (PDF). Colorado Secretary of State. May 28, 2019.
- "Top-to-Bottom Review". California Secretary of State. Retrieved July 8, 2020.
- CA SoS Top to Bottom Review Archived December 3, 2014, at the Wayback Machine Retrieved March 2, 2012
- Simons, Barbara. August 13, 2007. "California: The Top to Bottom Review." Archived February 25, 2016, at the Wayback Machine The Voter. Retrieved November 27, 2007.
- "Voting Technology Vendors". California Secretary of State. Retrieved July 8, 2020.
- Riordan, Theresa. September 13, 2006. "Archived copy". Archived from the original on March 4, 2016. Retrieved February 8, 2016.CS1 maint: archived copy as title (link) Princeton University. Retrieved March 6, 2008.
-
- ESS "Voting System Examination(s) And Status For Election Systems & Software, Inc". www.sos.state.tx.us. Retrieved December 3, 2020.
- Hart "Voting System Examination(s) And Status For Hart". www.sos.texas.gov. Retrieved December 3, 2020.
- Mechler, Brian (September 20, 2020). "Voting System Examination of Election Systems & Software EVS 6.1.1.0, section 7" (PDF). Texas Secretary of State. Retrieved December 3, 2020.
- "State Audit Laws". Verified Voting. Retrieved July 8, 2020.
- Benaloh, Public Evidence from Secret Ballots; et al. (2017). Electronic voting : second International Joint Conference, E-Vote-ID 2017, Bregenz, Austria, October 24–27, 2017, proceedings. Cham, Switzerland. p. 122. ISBN 9783319686875. OCLC 1006721597.
- Turner, Karl (November 5, 2007). "Elections board workers take plea deal". Cleveland Plain Dealer. Retrieved August 17, 2019.
- Recount Now (January 11, 2017). "Report on the 2016 Presidential Recount in Clark County, Nevada. Page 20" (PDF). Internet Archive. Archived from the original (PDF) on August 12, 2019. Retrieved August 17, 2019.
- "Voter views on U.S. election security". Pew Research Center - U.S. Politics & Policy. October 29, 2018. Retrieved August 5, 2020.
- Stewart, Charles (March 8, 2018). "What does "election hacking" mean to the public?". electionupdates.caltech.edu. Retrieved August 5, 2020.
- Tomz, Michael, Jessica L. P. Weeks (August 2019). "Public Opinion and Foreign Electoral Intervention" (PDF). Stanford University. Retrieved August 4, 2020.
- "Russia". www.pollingreport.com. May 16–20, 2019. Retrieved August 5, 2020.
- Bose, Nandita (October 15, 2019). "How Amazon.com moved into the business of U.S. elections". Reuters. Retrieved July 31, 2020.
- Heilweil, Rebecca (December 2, 2017). "Nine Companies That Want To Revolutionize Voting Technology". Forbes. Retrieved December 4, 2018.
- Malone, Claire (July 13, 2018). "What The Latest Mueller Indictment Tells Us About Election Hacking". FiveThirtyEight.
The Intercept report was based on National Security Agency documents, which did not directly identify the company but made references to a product made by VR Systems, whose products are used in eight states.
- Donovan, Doug (August 7, 2018). "Maryland senators ask Treasury panel to investigate Russian oligarch's ties to state election contractor - Baltimore Sun". Baltimore Sun. Archived from the original on August 10, 2018. Retrieved July 30, 2020.
- E. G. Arnold, History of Voting Systems in California Archived March 6, 2016, at the Wayback Machine, California Secretary of State Bill Jones, June 1999.
- Douglas W. Jones and Barbara Simons, Broken Ballots, CSLI Publications, 2012; see Section 5.2, page 96.
- "How E-voting Works". HowStuffWorks. Archived from the original on July 3, 2015.
- "Electronic Voting". Archived from the original on May 6, 2015.
- "Historical Timeline". Retrieved February 25, 2015.
- "Archived copy". Archived from the original on May 15, 2015. Retrieved May 22, 2015.CS1 maint: archived copy as title (link)
- "Voter Empowerment Act of 2013 (2013; 113th Congress H.R. 12) - GovTrack.us". GovTrack.us. Archived from the original on October 18, 2015.
- Zetter, Kim; Maiberg, Emanuel (March 14, 2019). "DARPA Is Building a $10 Million, Open Source, Secure Voting System". Vice. Retrieved June 1, 2019.
- "DARPA is trying to build an unhackable open-source voting system". MIT Technology Review. March 15, 2019. Retrieved June 1, 2019.
- Robitzski, Dan (March 14, 2019). "DARPA is building an open source voting machine". Futurism. Retrieved June 1, 2019.
- "Legislative Committee Resolution Awaiting BOD Approval" Archived July 24, 2011, at the Wayback Machine. (July 2004). Information Executive
- http://www.aitp.org/newsletter/2004julaug/index.jsp?article=evote.htm Archived September 8, 2004, at the Wayback Machine
- http://www.aitp.org/newsletter Archived July 24, 2011, at the Wayback Machine
- Padgett, Tim (November 3, 2007). "Voting Out E-Voting Machines". TIME. Archived from the original on August 24, 2013. Retrieved February 6, 2014.
- "Bill Summary & Status - 110th Congress (2007–2008) - S.2295 - CRS Summary - THOMAS (Library of Congress)". Thomas.loc.gov. November 1, 2007. Archived from the original on October 18, 2015. Retrieved February 6, 2014.
- "Archived copy" (PDF). Archived from the original (PDF) on March 5, 2008. Retrieved March 6, 2008.CS1 maint: archived copy as title (link)
- "H.R.5036: Emergency Assistance for Secure Elections Act of 2008 - U.S. Congress". OpenCongress. April 15, 2008. Archived from the original on March 13, 2012. Retrieved February 6, 2014.